Microsoft Alerts on IRS-Themed Phishing Attacks Targeting 29,000 Users with Remote Access Malware
As the U.S. tax season approaches, cybercriminals are intensifying their efforts to exploit this period by launching sophisticated phishing campaigns. Microsoft has recently identified a surge in such attacks, with over 29,000 users across 10,000 organizations being targeted. These campaigns are not only designed to steal sensitive information but also to deploy remote monitoring and management (RMM) tools, granting attackers persistent access to compromised systems.
Exploitation of Tax Season Urgency
Cybercriminals are leveraging the urgency associated with tax deadlines to craft deceptive emails. These messages often masquerade as official communications from the Internal Revenue Service (IRS) or tax professionals, containing subject lines related to refund notices, payroll forms, or filing reminders. The primary objective is to deceive recipients into opening malicious attachments, scanning QR codes, or clicking on suspicious links.
Targeting Professionals with Access to Financial Data
While many phishing attempts aim at individuals, a significant portion of these campaigns specifically targets accountants and other professionals who handle sensitive financial documents. These individuals are accustomed to receiving tax-related emails, making them prime targets for attackers seeking access to financial data.
Deployment of Remote Monitoring and Management Tools
A notable aspect of these campaigns is the deployment of legitimate RMM tools such as ConnectWise ScreenConnect, Datto, and SimpleHelp. Once installed, these tools provide attackers with persistent access to the victim’s device, enabling them to monitor activities, exfiltrate data, and potentially deploy additional malware.
Detailed Breakdown of Recent Campaigns
1. Certified Public Accountant (CPA) Lures: Attackers are sending emails that appear to be from CPAs, directing recipients to phishing pages created using the Energy365 Phishing-as-a-Service (PhaaS) kit. These pages are designed to capture email credentials. The Energy365 kit is estimated to dispatch hundreds of thousands of malicious emails daily.
2. QR Code and W2 Lures: Approximately 100 organizations, primarily in the manufacturing, retail, and healthcare sectors in the U.S., have been targeted. Emails contain QR codes leading to phishing sites that mimic Microsoft 365 login pages, built using the SneakyLog (also known as Kratos) PhaaS platform. These sites aim to steal user credentials and two-factor authentication codes.
3. Tax-Themed Domains: Cybercriminals are registering domains with tax-related names to deceive users into clicking on malicious links under the guise of accessing updated tax forms. These links often lead to the installation of RMM tools like ScreenConnect.
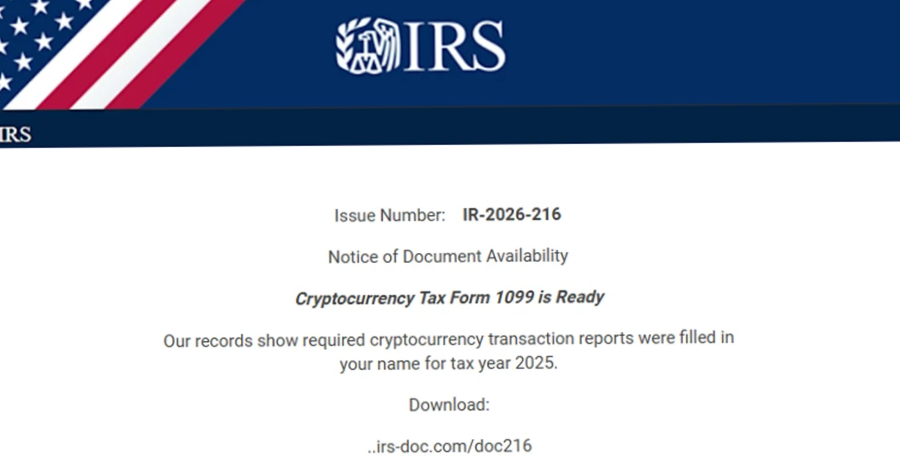
4. IRS Impersonation with Cryptocurrency Lures: In attacks targeting the higher education sector, emails impersonating the IRS instruct recipients to download a Cryptocurrency Tax Form 1099 from malicious domains such as irs-doc[.]com or gov-irs216[.]net. These sites deliver RMM tools like ScreenConnect or SimpleHelp.
5. Targeting Accountants for Tax Filing Assistance: Attackers send emails requesting help with tax filing, including malicious links that lead to the installation of Datto, another RMM tool.
Large-Scale Phishing Campaign on February 10, 2026
On February 10, 2026, a significant phishing campaign impacted over 29,000 users across 10,000 organizations. Approximately 95% of the targets were in the U.S., spanning industries such as financial services (19%), technology and software (18%), and retail and consumer goods (15%).
The phishing emails impersonated the IRS, claiming that irregular tax returns had been filed under the recipient’s Electronic Filing Identification Number (EFIN). Recipients were instructed to review these returns by downloading a purported IRS Transcript Viewer.
These emails, sent through Amazon Simple Email Service (SES), contained a Download IRS Transcript View 5.1 button. Clicking this button redirected users to smartvault[.]im, a domain masquerading as SmartVault, a legitimate document management platform. The phishing site utilized Cloudflare to evade automated scanners, ensuring that only human users received the malicious payload: a packaged version of ScreenConnect.
Recommendations for Mitigation
To protect against these sophisticated phishing campaigns, Microsoft recommends the following measures:
– Implement Multi-Factor Authentication (MFA): Enforce MFA across all accounts to add an extra layer of security.
– Educate Employees: Conduct regular training sessions to help employees recognize phishing attempts and understand the risks associated with clicking on unknown links or attachments.
– Monitor for Unusual Activity: Regularly review account activities for signs of unauthorized access or changes.
– Restrict RMM Tool Usage: Limit the use of RMM tools to authorized personnel and ensure they are configured securely.
– Stay Updated: Keep all systems and software up to date with the latest security patches.
By adopting these practices, organizations can enhance their defenses against the evolving tactics employed by cybercriminals during the tax season.