AstraZeneca Faces Alleged Data Breach by LAPSUS$ Group
In a recent development, the hacking group LAPSUS$ has reportedly claimed responsibility for a significant data breach involving AstraZeneca, a leading global pharmaceutical and biotechnology company. The group alleges to have accessed and exfiltrated approximately 3GB of internal data, which they are now attempting to sell.
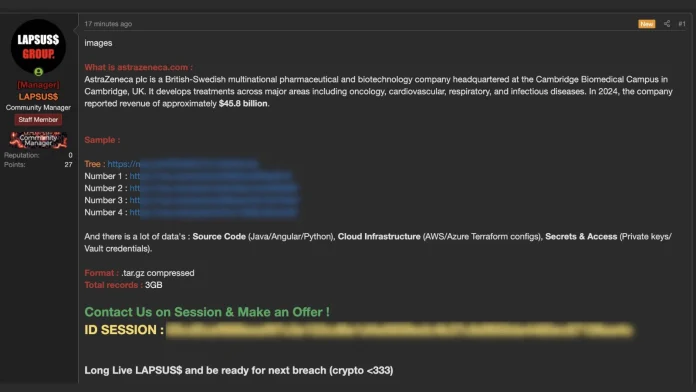
Details of the Alleged Breach
LAPSUS$, known for previous high-profile cyberattacks on major technology firms, has resurfaced with claims of infiltrating AstraZeneca’s internal systems. The group has posted teasers of the purported stolen data on illicit forums, detailing the contents of a compressed `.tar.gz` archive and providing screenshots as evidence.
The threat actors are seeking potential buyers through the secure messaging application Session, indicating a shift towards direct financial extortion rather than public data leaks. As of March 20, 2026, no full data leak has been made publicly available, suggesting the group’s primary motive is financial gain through direct sale.
Contents of the Alleged Data Dump
According to LAPSUS$’s claims on the breach forum, the 3GB data dump includes a wide array of sensitive information:
– Source Code: Java Spring Boot applications, Angular frontend frameworks, and various Python scripts.
– Cloud Infrastructure: Terraform configurations for AWS and Azure environments, alongside Ansible roles used for automation and orchestration.
– Secrets and Access Credentials: Private cryptographic keys, Vault credentials, and authentication tokens related to GitHub and Jenkins CI/CD pipelines.
To substantiate their claims, the attackers have released public samples revealing specific internal repository structures and project details. The exposed directory tree highlights a root folder named `AZU_EXFIL`, containing a critical supply-chain portal repository identified as `als-sc-portal-internal`.
This internal portal appears to manage several core logistical functions crucial to pharmaceutical distribution, including forecasting, inventory tracking, product master data management, SAP system integration, and On-Time In-Full (OTIF) delivery metrics.
Implications for AstraZeneca
If the claims are accurate, this breach could have far-reaching implications for AstraZeneca’s internal supply chain operations and overall cloud infrastructure security. The exposure of such sensitive information could potentially disrupt operations, compromise proprietary data, and erode stakeholder trust.
AstraZeneca’s Response
As of March 20, 2026, AstraZeneca has not publicly commented on the incident, and no official statement has been released. The company is likely conducting an internal investigation to assess the validity of the claims and determine the extent of any potential breach.
Broader Context
This alleged breach underscores the persistent threat posed by cybercriminal groups like LAPSUS$, who have previously targeted major corporations. It highlights the critical importance of robust cybersecurity measures, regular system audits, and employee training to mitigate the risk of such incidents.
Conclusion
While the full details and veracity of LAPSUS$’s claims remain to be confirmed, the situation serves as a stark reminder of the ever-present cyber threats facing organizations today. Companies must remain vigilant, proactively enhance their security postures, and be prepared to respond swiftly to potential breaches to protect their assets and maintain stakeholder confidence.