Perseus Android Malware: A New Threat Stealing User Notes and Enabling Full Device Takeover
A new Android banking trojan named Perseus has emerged, representing a significant advancement in mobile malware. Built upon the leaked source code of Cerberus and directly incorporating elements from the Phoenix codebase, Perseus enhances the capabilities of its predecessors. It combines credential theft, real-time device monitoring, and a unique ability to silently access personal notes stored on infected devices, positioning it as one of the most formidable Android threats currently active.
Distribution and Target Regions
Perseus primarily targets users in Turkey and Italy, with its reach extending to Poland, Germany, France, the United Arab Emirates, Portugal, and various cryptocurrency platforms. Cybercriminals distribute the malware through counterfeit IPTV applications, exploiting users’ familiarity with sideloading APK files to bypass the Google Play Store. By masquerading as legitimate streaming services, Perseus reduces user suspicion and increases infection rates. Additionally, a dropper application is employed to circumvent installation restrictions on Android 13 and later versions, complicating detection efforts.
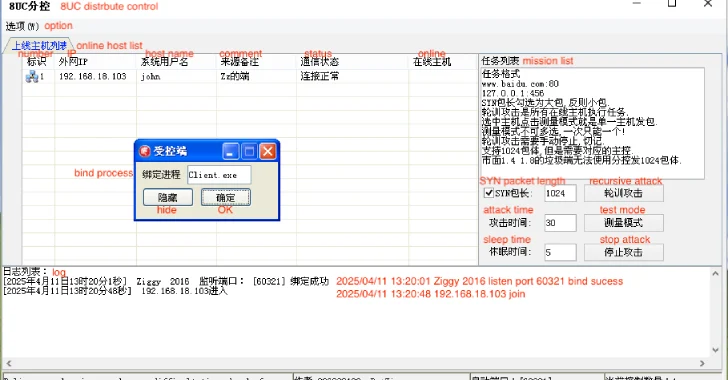
Technical Analysis and Infrastructure
ThreatFabric analysts identified Perseus as part of an active campaign, noting its connections to infrastructure shared with other known malware families, including Medusa and Klopatra. The malware’s name was derived from the command-and-control (C2) login panel observed during multiple campaign analyses, confirming its deliberate and purpose-built nature. Analysts identified two main variants: one written in English with extensive debugging features, and a more discreet Turkish-language version. Both variants actively target financial institutions and user data across multiple regions.
Operational Mechanisms
Upon installation, Perseus requests Accessibility Service permissions, which are central to its operation. These permissions enable the malware to monitor the screen, intercept user input, and simulate touch interactions without displaying any visible signs of activity. Perseus employs overlay attacks by presenting fake login pages over legitimate banking applications, while its keylogging capability records all user input. Combined with its remote control features, this grants attackers full interactive control over the compromised device, allowing them to conduct fraudulent activities and authorize transactions without the victim’s knowledge.
Scope and Impact
Perseus poses a significant financial threat, targeting over 50 institutions across eight countries and nine cryptocurrency platforms. Its ability to perform full device takeover while remaining undetected underscores the advanced nature of modern Android banking malware.
Unique Capability: Accessing User Notes
A distinguishing feature of Perseus is its ability to target note-taking applications on the victim’s device. Many users store sensitive information such as passwords, cryptocurrency recovery phrases, and financial account details in note apps, often unaware of the associated risks. Perseus exploits this vulnerability through a command called `scan_notes`, which identifies installed note applications and silently accesses their stored content without any user interaction.
Utilizing Android Accessibility Services, Perseus autonomously navigates each application’s interface. It opens individual notes, captures the text, and then returns to the previous screen before proceeding to the next note. This entire process operates silently in the background, leaving no visible indication for the victim. All captured note data is then transmitted to the attacker’s C2 server, providing them with access to a wealth of personal and potentially sensitive information.
Comparative Analysis with Other Android Malware
Perseus’s capabilities represent a significant evolution in Android malware. For instance, the TeaBot malware, discovered in 2021, was known for overlay attacks against banking applications to steal login credentials and credit card information. It also had the ability to send, intercept, and hide SMS messages, enable keylogging functionalities, steal Google Authentication codes, and obtain full remote control of an Android device via Accessibility Services and real-time screen-sharing. However, TeaBot did not exhibit the ability to access personal notes stored on the device, a feature that sets Perseus apart.
Similarly, the DCHSpy malware, identified in 2025, was capable of stealing WhatsApp data, call logs, recording audio, and taking photos. It spread via fake StarLink VPN apps on Telegram targeting dissidents. While DCHSpy demonstrated comprehensive data collection capabilities, it lacked the specific functionality to access and exfiltrate data from note-taking applications, a capability that Perseus uniquely possesses.
Mitigation Strategies
Given the sophisticated nature of Perseus, users are advised to exercise caution when downloading applications, especially from unofficial sources. To mitigate the risk of infection, consider the following strategies:
1. Download Applications from Trusted Sources: Always obtain apps from official app stores like Google Play, which have security measures in place to detect and remove malicious applications.
2. Verify App Authenticity: Before downloading, check the app’s developer information, reviews, and ratings to ensure its legitimacy.
3. Limit Permissions: Be cautious of apps requesting extensive permissions, particularly Accessibility Services, without a clear need.
4. Regular Updates: Keep your device’s operating system and applications updated to benefit from the latest security patches.
5. Install Security Software: Utilize reputable mobile security solutions that can detect and prevent malware infections.
6. Regular Backups: Maintain regular backups of important data to recover information in case of an infection.
7. User Education: Stay informed about the latest threats and educate yourself on safe online practices to reduce the risk of falling victim to malware.
Conclusion
Perseus represents a significant advancement in Android malware, combining traditional credential theft with innovative methods to access personal notes and achieve full device control. Its emergence underscores the need for heightened vigilance and proactive security measures among Android users. By adhering to best practices and staying informed about evolving threats, users can better protect themselves against such sophisticated malware campaigns.