Pyronut: Malicious Python Package Backdoors Telegram Bots with Remote Code Execution
In a recent cybersecurity incident, a malicious Python package named `pyronut` was discovered on the Python Package Index (PyPI), targeting developers who build Telegram bots. This package impersonated the widely-used `pyrogram` framework, which boasts approximately 370,000 monthly downloads, making it a prime target for such attacks.
Impersonation Tactics
Unlike typical typosquatting attacks that rely on slight misspellings of legitimate package names, the threat actor behind `pyronut` employed a more deceptive strategy. They replicated `pyrogram`’s entire project description verbatim, creating what researchers have termed a malicious fork. This approach aimed to deceive developers through social engineering, leading them to believe they were installing a legitimate package.
The `pyronut` package did not introduce any new features or functionalities. Its listed GitHub repository URL directed users to a non-existent page, indicating that the package was likely distributed through Telegram communities and developer forums rather than being discovered organically. Three versions of `pyronut` were published—2.0.184, 2.0.185, and 2.0.186—all containing malicious code.
Discovery and Response
On March 18, 2026, researchers from Endor Labs identified all three versions of `pyronut` on the same day they appeared on PyPI. They acted swiftly to have the packages quarantined within hours, significantly reducing the potential number of affected developers. However, any developer who ran their bot using `pyronut` during this brief window was fully exposed to compromise.
Stealthy Activation Mechanism
What set `pyronut` apart from many other malicious packages was its stealthy activation mechanism. Instead of executing harmful code during installation—a common tactic that can trigger security alerts—`pyronut` remained dormant until the developer ran their bot. It embedded a concealed backdoor module at `pyrogram/helpers/secret.py`, which loaded silently each time the Telegram client started, effectively bypassing standard install-time security checks.
Operational Details of the Backdoor
The backdoor was designed to activate when a developer invoked the `Client.start()` method, a fundamental step in initializing any `pyrogram`-based Telegram bot. The attacker had modified this method within `pyrogram/methods/utilities/start.py` to import and execute the hidden `secret.py` module each time a client started. To avoid detection, the entire call was encapsulated in a bare `try/except: pass` block, ensuring that any errors encountered by the backdoor would fail silently, allowing the bot to continue running without raising suspicion.
Once activated, the backdoor registered two hidden message handlers on the victim’s Telegram client, linked to two hardcoded attacker account IDs. The first handler, triggered by the `/e` command, utilized the `meval` library to execute arbitrary Python code within the live session, granting the attacker full access to messages, contacts, and Telegram API functions. The second handler, `/shell`, passed commands directly to `/bin/bash` via subprocess, providing the attacker with unrestricted system access. Notably, the backdoor was programmed to skip installation on the attacker’s own accounts, a clear indication of deliberate malicious intent.
Potential Consequences
The implications of a successful `pyronut` infection are severe. By gaining dual Remote Code Execution (RCE) capabilities, the attacker could:
– Steal Credentials: Access and exfiltrate sensitive information such as API keys, passwords, and personal data.
– Exfiltrate Data: Extract confidential data from the victim’s system, including messages, contacts, and files.
– Achieve Lateral Movement: Navigate through the victim’s network to compromise additional systems.
– Take Over Active Sessions: Gain control over the victim’s active Telegram session, potentially leading to further exploitation.
Broader Context of Supply Chain Attacks
The `pyronut` incident is part of a growing trend of supply chain attacks targeting developers through malicious packages. Similar attacks have been observed across various ecosystems:
– NPM Ecosystem: Malicious packages have been discovered that mimic legitimate utilities while harboring destructive backdoors capable of wiping entire production environments. ([cybersecuritynews.com](https://cybersecuritynews.com/malicious-npm-packages-as-utilities/?utm_source=openai))
– Go Programming Community: Malicious Go packages have been identified that mimic Google’s UUID library to exfiltrate sensitive data. ([cybersecuritynews.com](https://cybersecuritynews.com/malicious-go-packages-as-googles-uuid-library/?utm_source=openai))
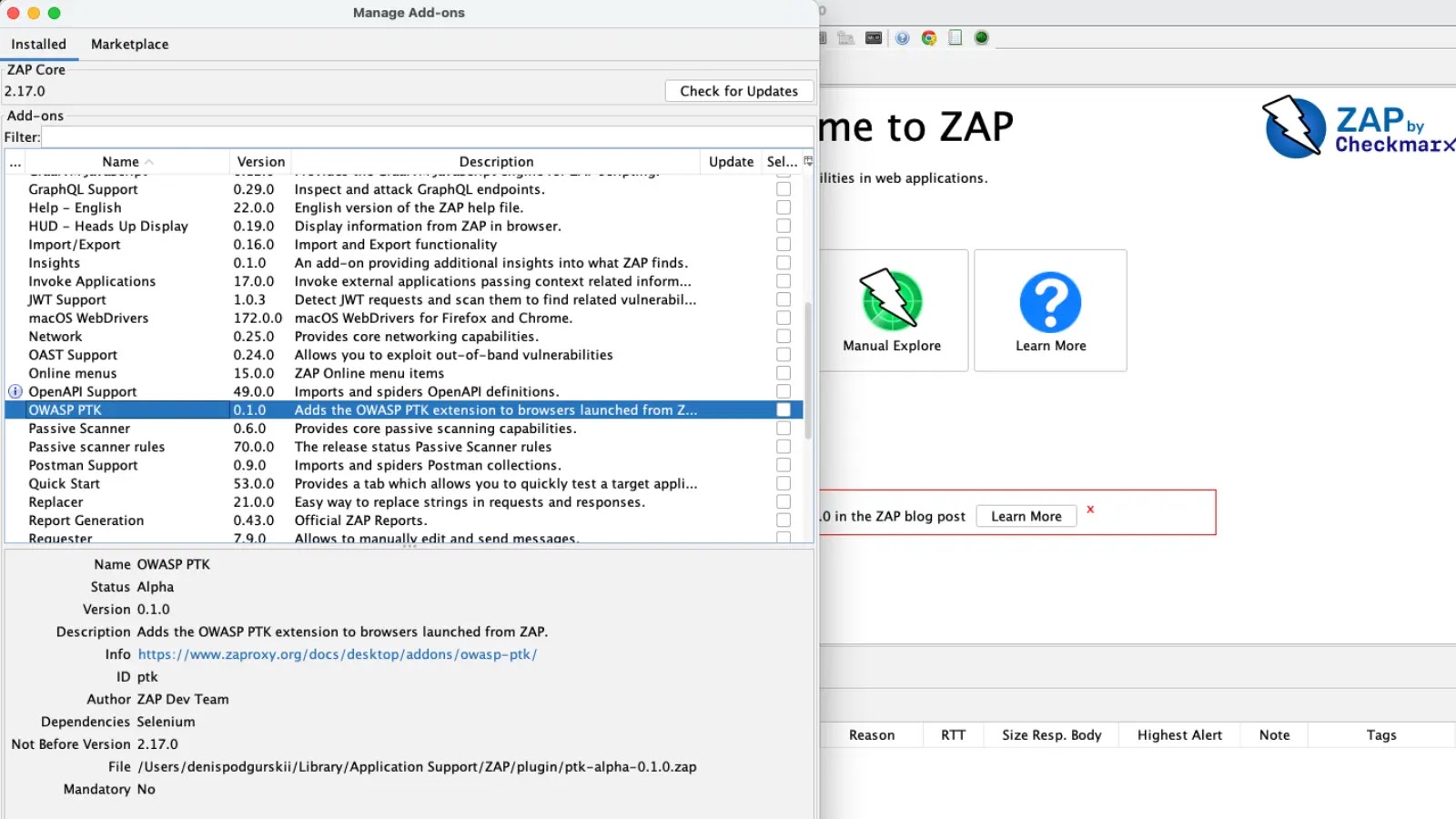
– Visual Studio Code Extensions: Malicious extensions posing as popular themes have been used to attack Windows and macOS users, turning the add-ons into hidden backdoors. ([cybersecuritynews.com](https://cybersecuritynews.com/malicious-vs-code-extension-as-icon-theme/?utm_source=openai))
Recommendations for Developers
To mitigate the risk of such attacks, developers are advised to:
1. Verify Package Authenticity: Always confirm the legitimacy of packages by checking official documentation and repository links.
2. Monitor for Suspicious Activity: Regularly review project dependencies and be alert to any unexpected behavior in applications.
3. Implement Security Best Practices: Utilize tools and services that scan for vulnerabilities in dependencies and provide alerts for potential threats.
4. Stay Informed: Keep abreast of the latest security advisories and reports to be aware of emerging threats.
By adopting these practices, developers can enhance the security of their projects and reduce the likelihood of falling victim to similar supply chain attacks.