Interlock Ransomware Exploits Cisco FMC Zero-Day Vulnerability for Root Access
In a significant cybersecurity development, Amazon Threat Intelligence has identified an active campaign by the Interlock ransomware group exploiting a critical vulnerability in Cisco’s Secure Firewall Management Center (FMC) Software. This flaw, designated as CVE-2026-20131 with a maximum CVSS severity score of 10.0, allows unauthenticated remote attackers to execute arbitrary Java code with root privileges on affected devices.
Understanding CVE-2026-20131
The vulnerability arises from insecure deserialization of user-supplied Java byte streams within the web-based management interface of Cisco’s Secure FMC Software. By sending a specially crafted serialized Java object to this interface, attackers can exploit the flaw to execute arbitrary code on the device, effectively gaining root-level access. This level of control enables attackers to manipulate system configurations, deploy malicious payloads, and potentially disrupt network operations.
Timeline of Exploitation
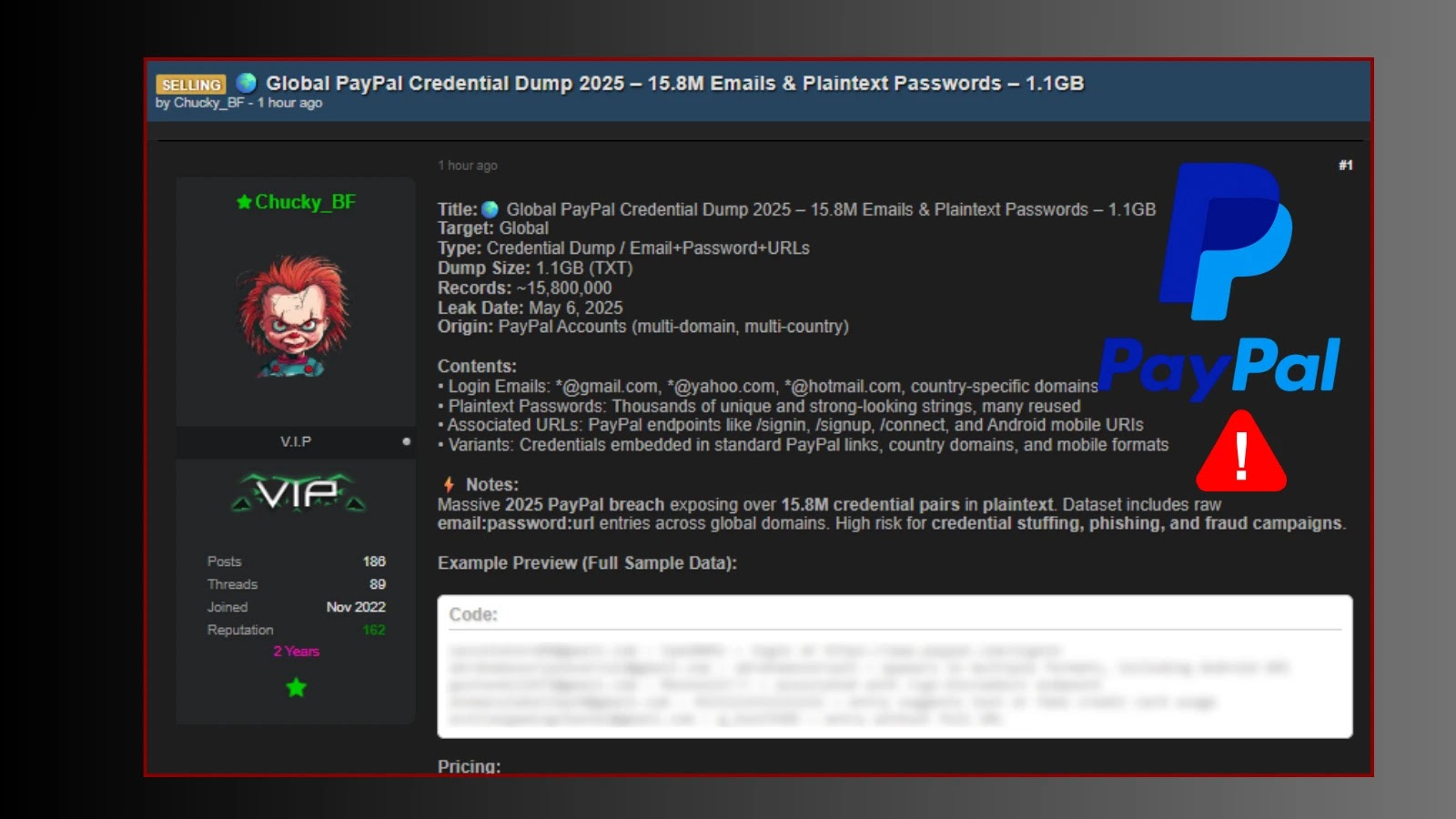
According to data from Amazon’s global sensor network, the Interlock ransomware group began exploiting this zero-day vulnerability on January 26, 2026, over a month before Cisco publicly disclosed the issue on March 4, 2026. This early exploitation provided the attackers with a significant advantage, allowing them to compromise systems before patches were available or administrators were aware of the threat.
Discovery and Disclosure
The exploitation was uncovered due to an operational security lapse by the threat actors, which exposed their toolkit through a misconfigured server. This exposure provided Amazon’s security team with valuable insights into the attack chain, including the tools and techniques employed by Interlock. Upon discovery, Amazon promptly shared their findings with Cisco to aid in the investigation and to expedite protective measures for customers.
Attack Chain Analysis
The attack sequence initiated with the transmission of crafted HTTP requests to a specific endpoint in the vulnerable software, aiming to execute arbitrary Java code. Following successful exploitation, the compromised system would send an HTTP PUT request to an external server, confirming the breach. Subsequent commands were then issued to download an ELF binary from a remote server, which hosted additional tools associated with the Interlock group.
Tools and Techniques Employed
The Interlock group’s toolkit comprises several sophisticated components:
– PowerShell Reconnaissance Script: This script systematically enumerates Windows environments, collecting data on operating systems, hardware configurations, running services, installed software, storage setups, virtual machines, user files, browser artifacts, network connections, and Remote Desktop Protocol (RDP) authentication events.
– Custom Remote Access Trojans (RATs): Developed in JavaScript and Java, these RATs facilitate command-and-control operations, interactive shell access, arbitrary command execution, file transfers, and SOCKS5 proxy capabilities. They also feature self-update and self-delete functions to evade detection and complicate forensic analysis.
– Bash Script for Proxy Configuration: This script configures Linux servers as HTTP reverse proxies to mask the attackers’ origins. It deploys ‘fail2ban,’ an open-source intrusion prevention tool, and sets up an HAProxy instance to forward inbound HTTP traffic to a specified target IP address. Additionally, it includes routines to erase logs and suppress shell history, enhancing stealth.
– Memory-Resident Web Shell: This component inspects incoming requests for specific parameters containing encrypted command payloads, which are then decrypted and executed, allowing for persistent access and control.
Implications for Organizations
The exploitation of CVE-2026-20131 by the Interlock ransomware group underscores the critical importance of timely vulnerability management and patching. Organizations utilizing Cisco’s Secure FMC Software are at heightened risk, as successful exploitation can lead to complete system compromise, data exfiltration, and operational disruptions.
Mitigation Strategies
To defend against such threats, organizations should implement the following measures:
1. Immediate Patch Application: Apply Cisco’s security updates addressing CVE-2026-20131 without delay to remediate the vulnerability.
2. Access Controls: Restrict access to the FMC web-based management interface to trusted networks and authorized personnel only.
3. Network Segmentation: Isolate management interfaces from production networks to limit potential attack vectors.
4. Monitoring and Logging: Implement comprehensive monitoring to detect unusual activities and maintain detailed logs for forensic analysis.
5. Incident Response Planning: Develop and regularly update incident response plans to ensure swift action in the event of a security breach.
Conclusion
The proactive identification and disclosure of this exploitation by Amazon Threat Intelligence highlight the evolving nature of cyber threats and the necessity for vigilant security practices. Organizations must prioritize the application of security patches, enforce strict access controls, and maintain robust monitoring systems to safeguard against such sophisticated attacks.