Cybercriminals Exploit SEO to Distribute Trojanized VPN Clients
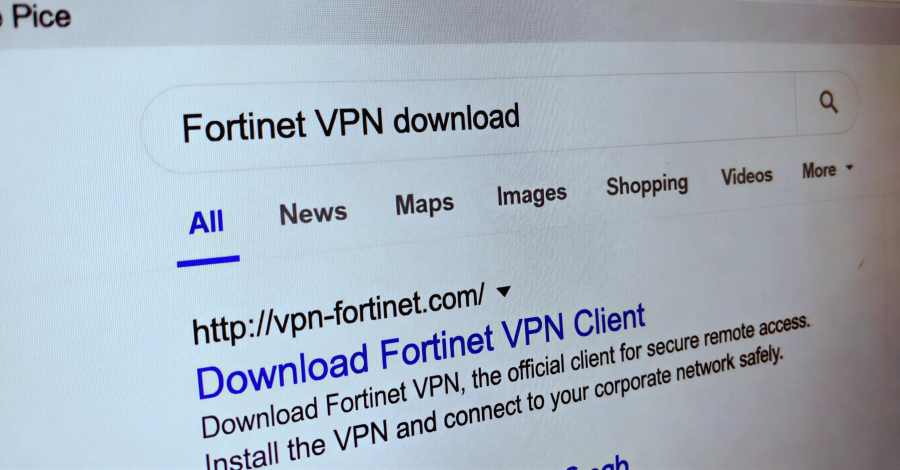
In a recent disclosure, Microsoft has unveiled a sophisticated credential theft campaign orchestrated by the threat actor identified as Storm-2561. This campaign leverages search engine optimization (SEO) poisoning to distribute malicious virtual private network (VPN) clients, aiming to harvest sensitive user credentials.
Modus Operandi of Storm-2561
The attackers employ SEO poisoning techniques to manipulate search engine results, directing users seeking legitimate enterprise software to malicious websites under their control. These sites host ZIP files containing digitally signed trojans that masquerade as trusted VPN clients. Upon installation, these trojans harvest VPN credentials from unsuspecting users.
Microsoft’s Threat Intelligence and Defender Experts teams observed this activity beginning in mid-January 2026. Storm-2561, active since May 2025, has a history of disseminating malware through SEO poisoning and impersonating reputable software vendors.
Evolution of the Attack Strategy
Initial reports by Cyjax highlighted Storm-2561’s use of SEO poisoning to redirect users searching for software from companies like SonicWall, Hanwha Vision, and Pulse Secure (now Ivanti Secure Access) to counterfeit sites. These sites tricked users into downloading MSI installers that deployed the Bumblebee loader, a known malware.
In October 2025, Zscaler documented a variant of this attack. Users searching for legitimate software on Bing were led to a fraudulent website (ivanti-vpn[.]org) offering a trojanized Ivanti Pulse Secure VPN client. This malicious client stole VPN credentials directly from the victim’s machine.
Technical Details of the Current Campaign
In the latest campaign, Storm-2561 exploits the trust users place in search engine rankings and software branding. By hosting malicious installer files on trusted platforms like GitHub, the attackers enhance the perceived legitimacy of their offerings.
The GitHub repository in question contains a ZIP file with an MSI installer that appears to be a legitimate VPN application. However, during installation, it sideloads malicious DLL files. The primary objective is to collect and exfiltrate VPN credentials using a variant of the information stealer known as Hyrax.
To deceive users, the malware displays a fake VPN sign-in dialog. When victims enter their credentials, they receive an error message and are prompted to download the genuine VPN client. In some instances, they are redirected to the legitimate VPN website, further masking the malicious activity.
For persistence, the malware utilizes the Windows RunOnce registry key, ensuring execution upon each system reboot.
Mitigation and Recommendations
Microsoft has taken steps to neutralize this operation by removing the malicious GitHub repositories and revoking the associated legitimate certificate.
To protect against such threats, organizations and individuals should:
– Implement Multi-Factor Authentication (MFA): Enhance account security by requiring multiple forms of verification.
– Exercise Caution with Downloads: Only download software from official and reputable sources.
– Verify Authenticity: Ensure the legitimacy of software by cross-referencing with official vendor websites.
By adopting these practices, users can significantly reduce the risk of falling victim to similar credential theft campaigns.