Chinese Cyber Espionage Targets Southeast Asian Militaries with Advanced Malware
A sophisticated cyber espionage campaign, attributed to a China-based threat actor, has been actively targeting military organizations in Southeast Asia since at least 2020. This state-sponsored operation, identified by Palo Alto Networks Unit 42 as CL-STA-1087, exhibits a high degree of strategic patience and precision, focusing on the collection of sensitive military intelligence rather than indiscriminate data theft.
Strategic Objectives and Operational Tactics
The primary aim of this campaign is to infiltrate military networks to gather intelligence on military capabilities, organizational structures, and collaborations with Western armed forces. The attackers demonstrate a methodical approach, employing custom malware and sophisticated techniques to maintain prolonged access to compromised systems.
Malware Arsenal: AppleChris and MemFun
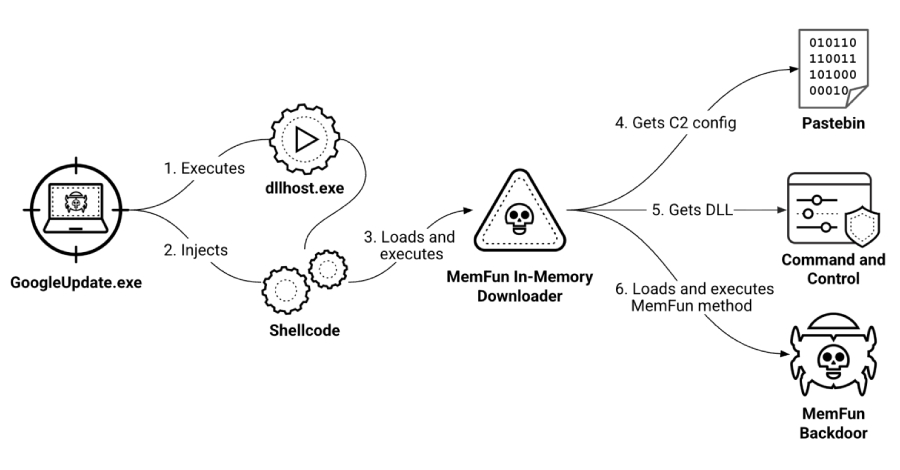
Central to the operation are two custom backdoors, AppleChris and MemFun, along with a credential harvesting tool named Getpass. These tools are designed to establish and maintain unauthorized access, facilitate data exfiltration, and evade detection.
Infection Vector and Persistence Mechanisms
The exact initial access method remains undetermined. However, the attack sequence involves deploying AppleChris variants across multiple endpoints following lateral movement within the network. This strategy ensures persistence and minimizes the likelihood of detection by signature-based security systems.
Command-and-Control Infrastructure
Both AppleChris and MemFun utilize a shared Pastebin account as a dead drop resolver to retrieve command-and-control (C2) addresses encoded in Base64. One variant of AppleChris also leverages Dropbox for this purpose, with Pastebin serving as a fallback. The use of legitimate services for C2 communication underscores the attackers’ efforts to blend malicious traffic with normal network activity, thereby evading detection.
Advanced Evasion Techniques
To circumvent automated security measures, the malware incorporates sandbox evasion tactics. These include implementing sleep timers—30 seconds for executable files and 120 seconds for DLLs—to delay execution and outlast typical monitoring periods of automated analysis tools.
Implications and Recommendations
This campaign highlights the persistent and evolving nature of state-sponsored cyber threats targeting military entities. Organizations are advised to enhance their cybersecurity posture by implementing robust monitoring systems, conducting regular security audits, and educating personnel on recognizing and responding to sophisticated cyber threats.