Critical Cisco SD-WAN Zero-Day Exploited Since 2023: A Call for Immediate Action
In a significant cybersecurity development, Cisco has disclosed a critical zero-day vulnerability, identified as CVE-2026-20127, affecting its Catalyst SD-WAN Controller and Manager. This flaw has been actively exploited by a sophisticated threat actor, designated UAT-8616, since at least 2023. The vulnerability, carrying a maximum CVSS score of 10.0, enables unauthenticated remote attackers to bypass authentication mechanisms, granting them administrative privileges on compromised systems.
Understanding the Vulnerability
The root cause of CVE-2026-20127 lies in a malfunctioning peering authentication mechanism within the affected Cisco Catalyst SD-WAN products. By sending specially crafted requests, attackers can exploit this flaw to log in as high-privileged, non-root internal users. Once inside, they gain access to the NETCONF interface, allowing them to manipulate the entire SD-WAN fabric’s network configuration. This includes adding rogue peers and altering routing protocols, effectively granting them control over the network’s operations.
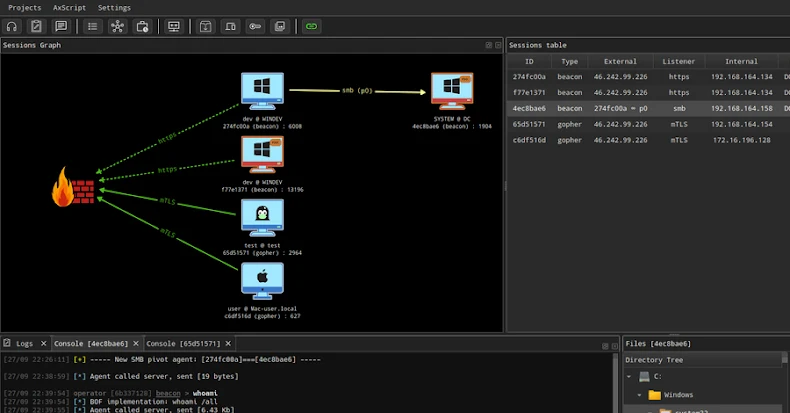
Exploitation Tactics
The threat actor UAT-8616 has demonstrated a high level of sophistication in exploiting this vulnerability. Their attack methodology involves downgrading the SD-WAN system to a version susceptible to the flaw, thereby gaining root access. Subsequently, they restore the original firmware to evade detection, ensuring persistent access to the compromised network. This tactic not only facilitates unauthorized control but also complicates forensic investigations aimed at identifying the breach.
Global Response and Mitigation Efforts
The severity of this vulnerability has prompted immediate action from global cybersecurity agencies. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-20127 to its Known Exploited Vulnerabilities catalog, mandating that Federal Civilian Executive Branch agencies remediate the issue within two days. This underscores the critical nature of the threat and the urgency required in addressing it.
Cisco has responded by releasing security updates and a comprehensive hardening guide to assist organizations in mitigating the risk. They recommend auditing internet-facing components, monitoring for unauthorized control connection peering events, and implementing robust access controls. Organizations are urged to apply these patches promptly and review their network configurations to identify any signs of compromise.
Broader Implications
This incident highlights the persistent and evolving threats targeting critical network infrastructure. The exploitation of such a significant vulnerability over an extended period underscores the need for continuous vigilance, timely patch management, and proactive security measures. Organizations must prioritize the security of their SD-WAN deployments, ensuring that they are not only up-to-date but also configured to minimize exposure to potential attacks.
Conclusion
The active exploitation of CVE-2026-20127 serves as a stark reminder of the importance of cybersecurity diligence. Organizations utilizing Cisco’s SD-WAN solutions must act swiftly to apply the necessary patches and review their security postures. By doing so, they can protect their networks from unauthorized access and maintain the integrity of their operations in the face of sophisticated cyber threats.