Critical Cisco SD-WAN Zero-Day Vulnerability Exploited Since 2023 Grants Root Access
Cisco has recently disclosed a critical zero-day vulnerability, identified as CVE-2026-20127, affecting its Catalyst SD-WAN products. This flaw has been actively exploited since at least 2023, allowing unauthenticated remote attackers to bypass authentication mechanisms and gain administrative privileges, potentially leading to full control over affected systems.
Vulnerability Overview
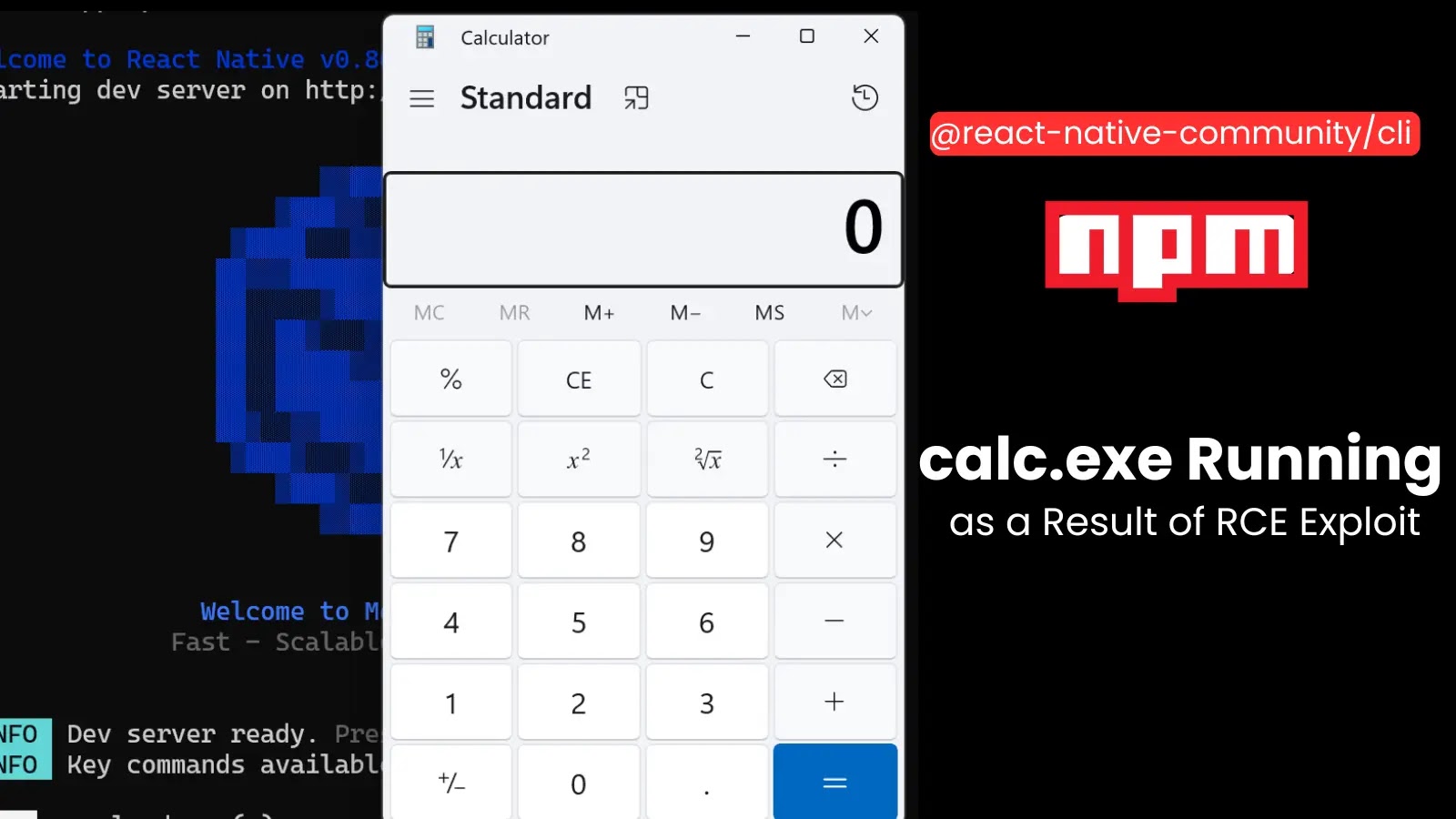
CVE-2026-20127 resides in the peering authentication mechanism of Cisco Catalyst SD-WAN Controller (formerly vSmart) and Cisco Catalyst SD-WAN Manager (formerly vManage). By sending specially crafted requests, attackers can circumvent authentication checks, logging in as high-privileged, non-root internal users. This access enables manipulation of the entire SD-WAN fabric’s network configuration through NETCONF, including the addition of rogue peers and alteration of routing protocols.
The vulnerability carries a CVSS v3.1 base score of 10.0, indicating its critical severity. It affects both on-premises deployments and Cisco-hosted SD-WAN Cloud environments, encompassing standard, managed, and FedRAMP setups. Cisco released patches on February 25, 2026, but confirmed that no workarounds exist.
Exploitation Timeline and Threat Actor Activity
Cisco Talos has been tracking a sophisticated threat actor, designated as UAT-8616, exploiting this vulnerability since at least 2023. The attackers have been adding malicious rogue peers to configurations, enabling long-term network access and persistence.
After bypassing authentication, the threat actors reportedly downgraded software versions to exploit CVE-2022-20775, a path-traversal flaw, for root escalation. They then restored the original software versions to evade detection. This chain of actions highlights the sophisticated tactics employed to target network edge devices for establishing footholds.
Incidents reported by intelligence partners confirm the compromise of internet-exposed management and control planes. Cisco Talos attributes these attacks to UAT-8616, assessed as a highly sophisticated actor with high confidence. The group focuses on SD-WAN for persistent access in critical sectors, continuing a trend of targeting edge devices.
Mitigation Steps
Organizations are urged to take immediate action to mitigate the risks associated with CVE-2026-20127:
1. Apply Patches: Immediately apply the patches provided by Cisco to address the vulnerability.
2. Inventory SD-WAN Deployments: Conduct a thorough inventory of all SD-WAN deployments, with a focus on internet-facing controllers.
3. Scan for Rogue Peers: Utilize the command `show sdwan omp peers detail` to scan for unauthorized peers and review NETCONF sessions for anomalies.
4. Enable Logging: Activate logging for authentication failures and version changes; reset compromised configurations if detected.
5. Restrict Management Access: Implement restrictions on management plane access to minimize exposure.
6. Monitor for Indicators of Compromise: Regularly monitor logs and configurations for signs of unauthorized access or changes.
Given the active exploitation and the critical nature of this vulnerability, organizations, especially those in critical infrastructure sectors, should prioritize these mitigation steps to secure their networks against potential attacks.