Enhancing Cybersecurity: Addressing the Pitfalls of Ineffective Triage
In the realm of cybersecurity, triage is intended to streamline the process of identifying and addressing threats. However, when triage processes are flawed, they can inadvertently escalate business risks rather than mitigate them. This article explores five common triage issues that can transform investigations into costly guesswork and offers strategies to rectify these challenges using execution evidence.
1. Decisions Made Without Concrete Evidence
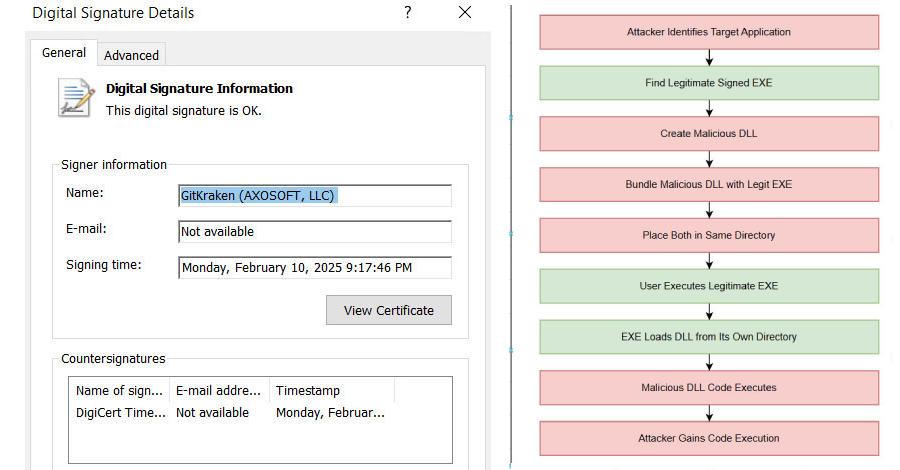
Business Risk: One of the most insidious failures in triage is making decisions without solid proof. When responders depend on incomplete signals—such as labels, hash matches, or reputational data—they may approve or escalate cases without fully understanding the behavior of a file or link. This uncertainty can lead to false positives, overlooked genuine threats, delayed containment, and increased costs per case, all while providing attackers with more time before a definitive verdict is reached.
Solution: To mitigate this risk, high-performing teams validate behavior during the triage phase. Utilizing sandboxes allows for real-time observation of execution, including process activities, network calls, persistence mechanisms, and the complete attack chain. For instance, with interactive sandbox tools like ANY.RUN, teams report that in approximately 90% of cases, they can visualize the full attack chain within about 60 seconds, enabling evidence-backed decisions early in the workflow.
Business Outcomes:
– Accelerated, evidence-based verdicts during triage
– Reduced costs per case by minimizing rework
– Decreased number of missed threats due to ambiguous closures
2. Triage Quality Dependent on Analyst Experience
Business Risk: In many Security Operations Centers (SOCs), the quality of triage is contingent upon the experience level of the analyst handling the alert. Senior staff can close cases more swiftly due to pattern recognition, whereas junior staff may escalate cases due to a lack of confidence or context. This disparity results in inconsistent verdicts, variable response times, and a workflow that becomes increasingly inefficient as alert volumes rise.
Solution: To address this issue, leading teams design triage processes centered around shared evidence and standardized procedures rather than individual experience. The objective is to equip Tier 1 analysts with sufficient clarity to reach the same conclusions as senior responders, based on observable facts. Tools like ANY.RUN facilitate this by allowing teams to share sandbox sessions and findings through built-in collaboration features, ensuring that knowledge is not siloed within individual team members.
Business Outcomes:
– Consistent triage outcomes across different shifts
– Reduced need for senior staff reviews
– More predictable Service Level Agreements (SLAs)
3. Delayed Triage Extends Attacker Dwell Time
Business Risk: Even when a threat is detected, prolonged triage processes can delay confirmation of the threat’s nature. Manual checks and queued escalations extend the time attackers have to move laterally or exfiltrate data. This delay manifests as missed SLAs and increased incident costs.
Solution: High-performing teams treat triage as a time-sensitive issue, aiming to minimize the steps between detection and a defensible verdict. This involves confirming behavior immediately, before the case undergoes multiple queues or validation loops. Interactive sandboxes enable rapid detonation of suspicious files and URLs, often revealing the full attack chain in under a minute. Operational results frequently show up to 21 minutes shaved off Mean Time to Respond (MTTR) per case, as teams spend less time waiting, re-checking, and escalating to confirm incidents.
Business Outcomes:
– Quicker confirmation leading to shorter attacker dwell time
– Fewer SLA breaches under high alert volumes
– Reduced impact of incidents
4. Over-Escalation Obscures Critical Incidents
Business Risk: When evidence is unclear, Tier 1 analysts may escalate cases just to be safe, turning Tier 2 into a verification layer for borderline cases. This practice clogs queues, diverts senior staff to ambiguous cases, and slows response to high-impact incidents, increasing investigation costs and the risk of critical cases being delayed.
Solution: Empowering Tier 1 analysts to independently prove or dismiss alerts allows Tier 2 to focus on genuine incidents rather than acting as a verification desk. Tools like ANY.RUN facilitate this by providing an intuitive sandbox designed for rapid triage, offering AI-assisted guidance during analysis, and generating automatic reports that capture key evidence without additional manual effort. A dedicated Indicators of Compromise (IOCs) tab consolidates indicators, enabling Tier 1 to escalate cases with context rather than for confirmation.
Business Outcomes:
– Reduced overload on Tier 2 analysts
– Faster processing of queues
– Lower volume of escalations
5. Manual Processes Limit Scalability and Increase Errors
Business Risk: Much of triage still involves repetitive manual tasks, such as following redirect chains, handling CAPTCHAs, or uncovering hidden links in QR codes. As alert volumes grow, this manual approach limits throughput, increases the likelihood of errors, and triggers unnecessary escalations due to time constraints.
Solution: Modern sandbox environments combine automation with human-like interactivity, allowing suspicious content to be safely opened, redirect flows to be followed, and protection mechanisms like CAPTCHAs or QR-embedded links to be handled automatically during analysis. With ANY.RUN’s interactive sandbox, these routine triage actions are performed within a controlled environment, exposing hidden malicious behavior while reducing repetitive work for responders. In daily operations, teams often experience up to a 20% decrease in Tier 1 workload, along with fewer escalations and more time available for high-value investigations.
Business Outcomes:
– Increased capacity for Tier 1 analysts
– Fewer manual errors
– More time allocated to confirmed threats
Conclusion:
Ineffective triage processes can subtly slow response times, increase escalation pressures, and allow real threats to persist longer than acceptable. Teams that transition to evidence-driven, execution-based triage consistently report measurable improvements, including:
– Up to a threefold increase in overall SOC efficiency
– 94% of users reporting faster triage and clearer verdicts
– Up to 58% more threats identified across investigations
Enhancing speed, certainty, and scalability at the triage stage is one of the most effective ways to reduce MTTR, control operational costs, and minimize real business exposure.