Bloody Wolf’s Cyber Onslaught: Expanding Java-Based NetSupport RAT Attacks in Central Asia
The cyber threat landscape in Central Asia has been significantly disrupted by the activities of a malicious group known as Bloody Wolf. Since June 2025, this group has orchestrated a series of sophisticated cyber attacks targeting Kyrgyzstan, with a primary objective of deploying the NetSupport Remote Access Trojan (RAT). By October 2025, their operations had expanded to include Uzbekistan, marking a concerning escalation in their regional cyber offensive.
Targeted Sectors and Methodology
Bloody Wolf’s campaign has been particularly aggressive against the finance, government, and information technology sectors. Their modus operandi involves impersonating official entities, notably the Ministry of Justice in Kyrgyzstan. They craft convincing PDF documents and utilize domain names that closely resemble legitimate government websites. These deceptive documents contain links to malicious Java Archive (JAR) files, which, when executed, deploy the NetSupport RAT onto the victim’s system.
Technical Execution of the Attacks
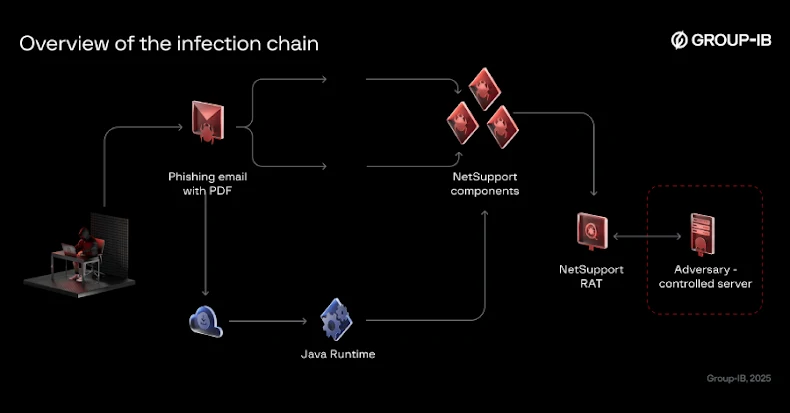
The attack sequence is meticulously designed to exploit user trust and system vulnerabilities:
1. Phishing Emails: Victims receive emails that appear to be from trusted government sources, urging them to open attached PDF documents.
2. Malicious Links: These PDFs contain links that, when clicked, download JAR files under the guise of necessary software updates or document viewers.
3. Java Runtime Installation: The emails often instruct recipients to install or update Java Runtime, claiming it’s essential for viewing the document. This step is crucial for executing the JAR file.
4. Payload Deployment: Once the JAR file is executed, it downloads and installs the NetSupport RAT from servers controlled by the attackers.
5. Persistence Mechanisms: To maintain control over the compromised system, the malware establishes persistence through:
– Scheduled Tasks: Creating tasks that run the malware at specified intervals.
– Registry Modifications: Adding entries to the Windows Registry to ensure the malware runs upon system startup.
– Startup Folder Scripts: Placing batch scripts in the startup folder to execute the malware when the system boots.
Geofencing Tactics in Uzbekistan
A notable aspect of the campaign in Uzbekistan is the implementation of geofencing techniques. This strategy ensures that only users within Uzbekistan are affected:
– Localized Targeting: Requests from IP addresses outside Uzbekistan are redirected to legitimate government websites, minimizing the risk of detection.
– Selective Malware Delivery: Only users within the country receive the malicious JAR file, enhancing the attack’s precision and effectiveness.
Technical Specifications of the Malware
The tools employed by Bloody Wolf reveal a reliance on older, yet effective, technologies:
– JAR Loaders: Built with Java 8, released in March 2014, indicating the use of outdated but functional software components.
– NetSupport RAT: The payload is an older version of NetSupport Manager from October 2013, suggesting a preference for tried-and-tested tools that may evade modern detection methods.
Implications and Recommendations
The expansion of Bloody Wolf’s activities underscores the evolving nature of cyber threats in Central Asia. Their ability to leverage low-cost, commercially available tools into sophisticated, regionally targeted operations highlights the need for heightened vigilance.
Recommendations for Organizations:
1. Employee Training: Conduct regular cybersecurity awareness programs to educate staff about phishing tactics and the importance of verifying email sources.
2. Software Updates: Ensure all systems are updated with the latest security patches to mitigate vulnerabilities exploited by older malware versions.
3. Email Filtering: Implement advanced email filtering solutions to detect and block phishing attempts.
4. Network Monitoring: Utilize intrusion detection systems to monitor for unusual network activity indicative of malware communication.
5. Access Controls: Restrict the execution of JAR files and enforce the principle of least privilege to limit the potential impact of an attack.
Conclusion
Bloody Wolf’s campaign exemplifies the persistent and adaptive nature of cyber threats. By exploiting trust in government institutions and utilizing straightforward yet effective malware delivery methods, they have managed to establish a significant foothold in the Central Asian cyber landscape. Organizations in the region must adopt a proactive and comprehensive approach to cybersecurity to defend against such evolving threats.