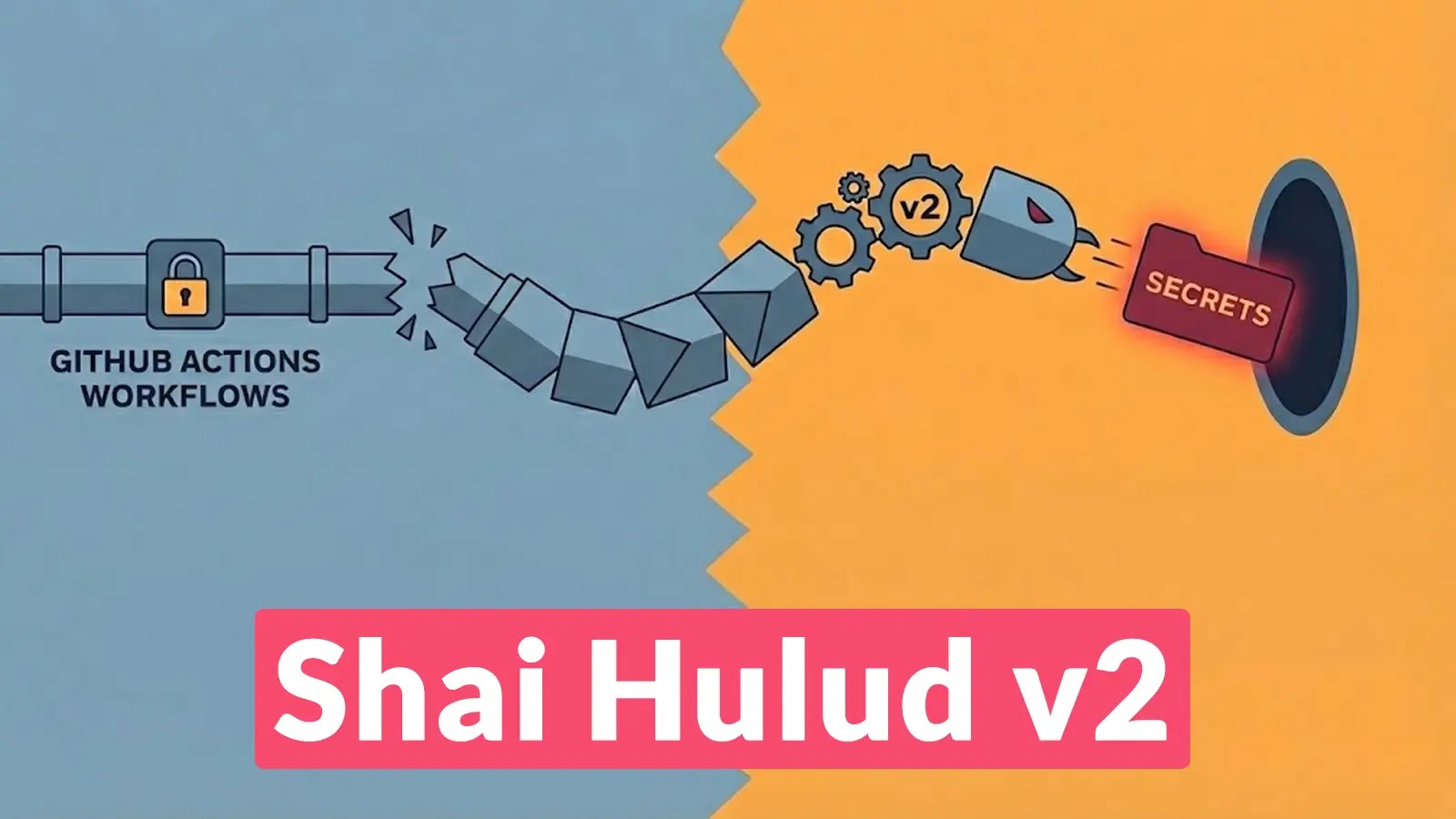
Shai Hulud v2: A Sophisticated Malware Campaign Exploiting GitHub Actions to Compromise Software Supply Chains
The software development community is currently facing a significant threat from Shai Hulud v2, a highly sophisticated malware campaign that has infiltrated 834 packages across the npm and Maven ecosystems. This campaign specifically targets GitHub Actions workflows, exploiting the `pull_request_target` trigger to inject malicious code into widely used libraries.
Understanding the Attack Mechanism
Shai Hulud v2 employs a multi-stage infection process:
1. Initial Compromise: The attackers gain access to repositories by exploiting vulnerabilities in GitHub Actions workflows, particularly those using the `pull_request_target` trigger. This trigger allows workflows to run with elevated permissions, providing an avenue for malicious code injection.
2. Stealthy Loader Deployment: A pre-install script named `setupbun.js` is introduced, which installs the Bun runtime. This runtime then executes an obfuscated payload, `bunenvironment.js`, while suppressing standard output to evade detection during build logs.
3. Privilege Escalation and Persistence: By infiltrating compromised Continuous Integration (CI) pipelines, the malware gains privileged access to repository secrets. This access enables it to modify source code, increment patch versions, and republish infected packages to public registries.
Notable Targets and Impact
The campaign has affected major projects, including PostHog, Zapier, and AsyncAPI. By leveraging compromised automation tokens, the malware systematically infects downstream dependencies, leading to a widespread impact on the software supply chain.
Unique Persistence Mechanism
Security analysts at Socket.dev have identified a distinctive persistence mechanism employed by Shai Hulud v2. The malware uses a beacon phrase, Sha1-Hulud The Second Coming, to search GitHub and re-trigger infections. This tactic ensures that even if individual repositories are cleaned, the attackers can locate and re-compromise vulnerable endpoints.
Credential Harvesting and Exfiltration
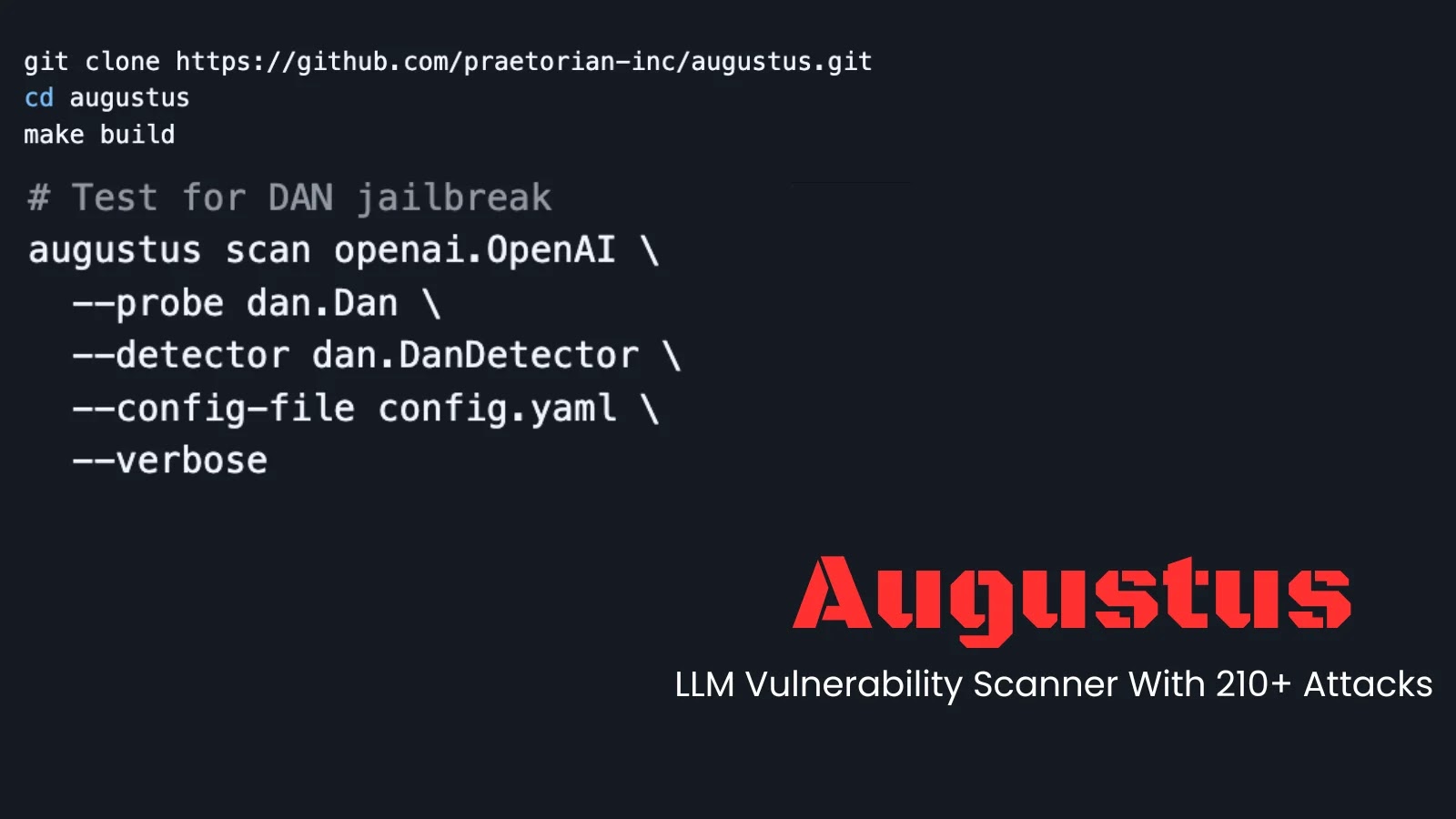
Once embedded in a CI environment, the malware executes a comprehensive credential harvesting routine:
– Environment Variable Capture: It captures all available environment variables, specifically targeting `GITHUB_TOKEN`, `NPM_TOKEN`, and `AWS_ACCESS_KEY_ID`.
– Filesystem Scanning: Deploying a TruffleHog binary, the malware scans the local filesystem for embedded secrets.
– Cloud Infrastructure Enumeration: Unlike typical scrapers, this payload aggressively enumerates cloud infrastructure, cycling through every region in AWS, Google Cloud, and Azure to extract secrets from managed vaults.
– Data Obfuscation and Exfiltration: All stolen data is obscured using three layers of Base64 encoding before being exfiltrated to a randomly generated GitHub repository created within the victim’s account.
Privilege Escalation and Destructive Actions
The malware attempts privilege escalation on Linux runners by manipulating `sudoers` or executing `Docker run –privileged` commands to gain root access. If no valid credentials are found to propagate the worm, the malware executes a destructive wiper function that deletes files, causing significant disruption to development environments.
Mitigation Strategies
To defend against such sophisticated attacks, organizations should implement the following strategies:
1. Review and Secure GitHub Actions Workflows: Carefully assess workflows, especially those using the `pull_request_target` trigger, to ensure they do not inadvertently grant elevated permissions to untrusted code.
2. Implement Least Privilege Principles: Limit the permissions granted to automation tokens and ensure that secrets are not exposed unnecessarily.
3. Monitor for Unusual Activity: Establish monitoring mechanisms to detect unusual activities, such as unexpected repository modifications or the creation of new repositories within organizational accounts.
4. Regularly Rotate Secrets: Implement a routine schedule for rotating secrets and tokens to minimize the risk of compromised credentials being exploited.
5. Educate Development Teams: Provide training to development teams on secure coding practices and the importance of scrutinizing third-party dependencies.
Conclusion
The emergence of Shai Hulud v2 underscores the evolving nature of threats targeting the software supply chain. By exploiting GitHub Actions workflows, attackers have demonstrated the potential for widespread compromise through automated processes. It is imperative for organizations to adopt robust security measures, continuously monitor their development environments, and foster a culture of security awareness to mitigate such risks.