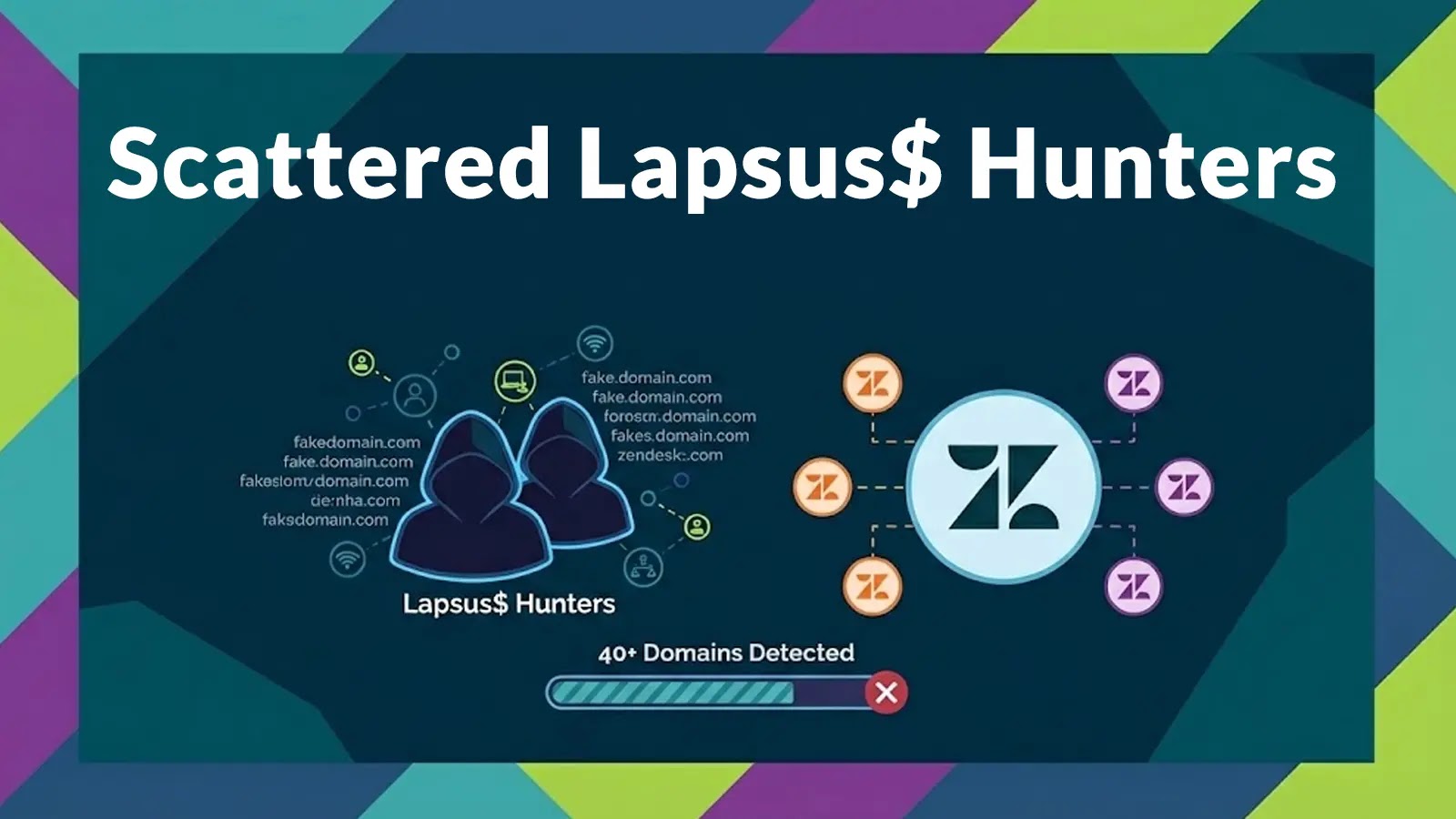
Cybercriminals Exploit Zendesk with Over 40 Deceptive Domains
A sophisticated cyberattack campaign has been launched by the group known as Scattered Lapsus$ Hunters, targeting Zendesk, a widely used customer support platform. This operation involves the registration of more than 40 deceptive domains designed to mimic legitimate Zendesk environments, aiming to harvest sensitive user credentials and infiltrate corporate networks.
Typosquatting Tactics
The attackers have employed a technique called typosquatting, where they register domains with slight misspellings or variations of legitimate ones. Examples include znedesk[.]com and vpn-zendesk[.]com. These counterfeit sites are meticulously crafted to resemble authentic Zendesk login pages, complete with Single Sign-On (SSO) portals. Unsuspecting users who enter their credentials on these sites inadvertently provide attackers with access to their accounts.
Infrastructure and Evasion Strategies
The campaign’s infrastructure reveals a coordinated effort to bypass standard detection protocols. The domains were consistently registered through NiceNic and use Cloudflare-masked nameservers to hide their true hosting origins. By using these hiding techniques, the actors ensure their phishing pages remain active long enough to harvest significant volumes of high-privilege credentials before defenders can react.
Weaponizing Support Tickets
A particularly insidious aspect of this campaign is the weaponization of legitimate support tickets. The attackers submit fraudulent tickets directly into an organization’s Zendesk portal, posing as urgent system administration requests or password reset inquiries. These tickets often contain links to the typosquatted domains or malicious payloads. When support agents interact with these tickets, they may inadvertently download Remote Access Trojans (RATs), granting attackers persistent remote control over the system.
Implications and Recommendations
The Scattered Lapsus$ Hunters have demonstrated a strategic evolution in their attack methods, combining typosquatting, sophisticated infrastructure evasion, and social engineering tactics. Organizations using Zendesk or similar platforms should be vigilant, implementing robust verification processes for support requests and educating employees about the risks of phishing and typosquatting. Regular monitoring of domain registrations and network traffic can also help in early detection and mitigation of such threats.