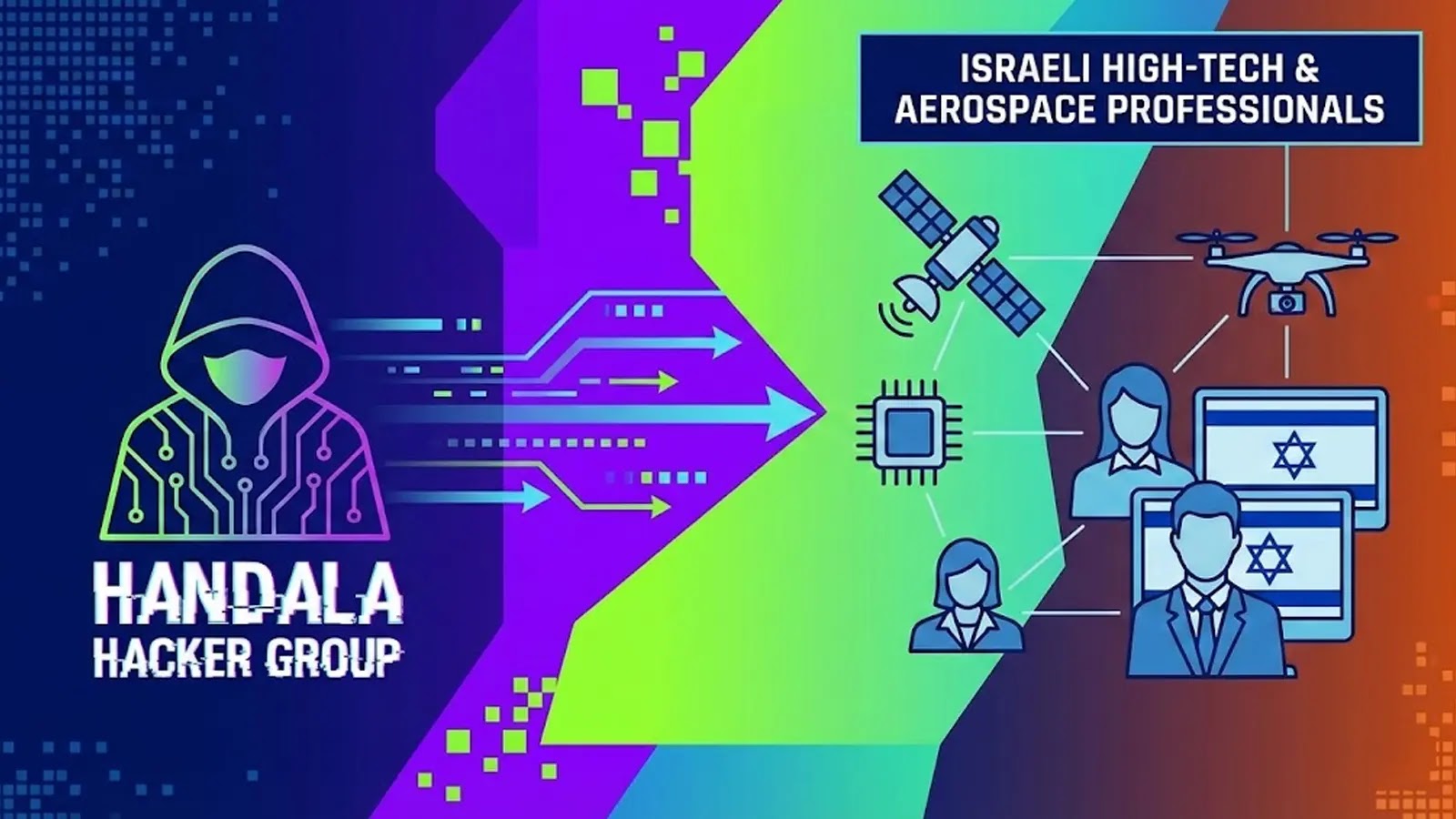
Handala Hacker Group Escalates Cyber Attacks on Israeli High-Tech and Aerospace Sectors
In a significant escalation of cyber warfare, the Handala hacker group has initiated a targeted campaign against Israeli professionals in the high-tech and aerospace industries. This development underscores the evolving nature of cyber threats, where state-sponsored and ideologically driven groups are increasingly focusing on private-sector individuals to achieve their objectives.
The Emergence of Handala’s Targeted Campaign
Handala, a pro-Palestinian hacktivist group, has recently published a list of Israeli individuals employed in critical sectors such as high technology and aerospace. Accompanying this list are hostile descriptions that falsely label these professionals as criminals, marking a shift from traditional propaganda to active doxxing and intelligence gathering. This strategy not only aims to intimidate the individuals but also seeks to disrupt the operations of key industries by targeting their human resources.
The Mechanics of the Attack
The group’s approach involves the public exposure of personal and professional information of Israeli specialists. This data was disseminated through their dark web platform, with financial incentives offered to those who could provide additional information about the targeted individuals. Such a bounty-style method creates a crowdsourced intelligence collection mechanism, amplifying the threat beyond the initial data leak and endangering ordinary professionals.
Trustwave security researchers identified this activity during their ongoing dark web monitoring operations. Their analysis revealed that the published dataset heavily relies on information scraped from LinkedIn profiles. However, several inconsistencies were noted, including individuals who had left their listed companies years ago, employees in non-sensitive roles, and profiles with no verifiable connection to the high-tech sector. These discrepancies suggest that Handala may be supplementing legitimate LinkedIn data with fabricated entries or information from unverifiable sources, thereby inflating their target list while maintaining a veneer of authenticity.
Data Manipulation and Weaponization Techniques
The technical analysis of Handala’s methods indicates a combination of automated data scraping and manual data manipulation. By indiscriminately collecting and publishing this information, the group demonstrates how publicly available data can be weaponized at scale. Framing ordinary workers as criminal targets and pairing this with financial incentives for additional intelligence creates a dangerous mechanism that poses direct risks to the privacy, safety, and professional reputations of legitimate employees.
Broader Context of Cyber Threats
This campaign by Handala is not an isolated incident but part of a broader trend of cyberattacks targeting Israeli entities. For instance, the Iranian APT35 group has been attacking high-profile cybersecurity experts and professors from Israel, employing deceptive social engineering tactics to steal sensitive information. Similarly, pro-Russian hacktivist groups have been targeting government portals, financial services, and online commerce platforms in Israel and allied nations, demonstrating unprecedented levels of organization and cross-ideological cooperation among geographically dispersed threat actors.
Moreover, during the 12-day conflict between Israel and Iran in June 2025, a sophisticated network of Iranian-linked cyber threat actors launched coordinated digital operations against critical infrastructure sectors worldwide. These operations targeted financial institutions, government agencies, and media organizations across multiple countries, highlighting the global nature of cyber threats.
Implications and Recommendations
The escalation of such targeted cyber campaigns has significant implications for both individuals and organizations. For individuals, especially those in sensitive sectors, it underscores the importance of maintaining strict personal data hygiene and being vigilant about the information shared on public platforms. Organizations, on the other hand, must implement continuous monitoring for identity-related threats and develop comprehensive awareness programs to educate employees about potential risks.
Furthermore, this incident highlights the need for robust cybersecurity measures within humanitarian organizations, as pro-Houthi groups like OilAlpha have been targeting such entities with malicious Android applications to steal credentials and gather intelligence. The persistent threat posed by cyberattacks against NGOs necessitates the implementation of strong security protocols to protect sensitive data and ensure the continuity of humanitarian operations.
In conclusion, the Handala hacker group’s recent activities represent a concerning shift in cyber warfare tactics, emphasizing the need for heightened vigilance and proactive measures to safeguard individuals and organizations against such threats.