Apple Releases Critical Security Update for Older iPhones and iPads to Counter DarkSword Exploits Apple has issued a vital security update targeting older iPhone and […]
Month: April 2026
Anthropic’s Source Code Leak Exposes AI Secrets, Sparks GitHub Takedown Controversy
Anthropic’s Accidental Source Code Leak and the Unintended GitHub Takedown In March 2026, Anthropic, a leading artificial intelligence company, inadvertently exposed over 500,000 lines of […]
Sonder Revolutionizes Online Dating with Authenticity and Creative Real-World Events
Sonder’s Unique Approach: Redefining Online Dating with Creativity and Authenticity In the crowded landscape of online dating, where profiles often blur into a monotonous stream […]
Critical Vulnerability in Vim Editor Allows OS Command Execution; Users Urged to Update to Version 9.2.0276
Critical Vulnerability in Vim Text Editor Allows Arbitrary OS Command Execution A significant security flaw has been identified in Vim, a widely used text editor […]
Critical Vulnerability in Nginx-UI Enables Remote Code Execution; Immediate Patch Recommended
Critical Nginx-UI Vulnerability Exposes Systems to Remote Code Execution A critical security vulnerability has been identified in Nginx-UI’s backup and restore functionality, designated as CVE-2026-33026. […]
Microsoft Teams to Strip EXIF Metadata from Images for Enhanced Privacy by 2026
Microsoft Teams Enhances Privacy by Removing EXIF Data from Shared Images In a significant move to bolster user privacy and security, Microsoft has announced that, […]
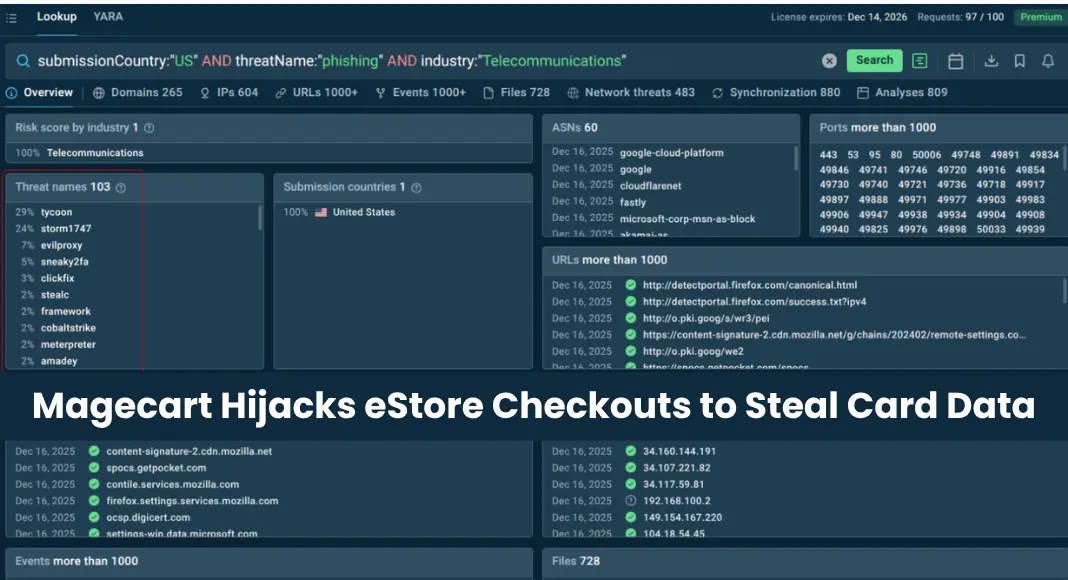
Magecart Hackers Exploit 100+ Domains to Steal Payment Data from E-commerce Sites Across 12 Countries
Magecart Hackers Exploit Over 100 Domains to Hijack eStore Checkouts and Steal Payment Data A sophisticated and prolonged Magecart campaign has been actively compromising e-commerce […]
HSBC India’s Uppercase Password Mandate Sparks Security Concerns Among Experts
HSBC India’s Uppercase Password Policy Raises Security Concerns Starting April 6, 2026, HSBC India will mandate that all internet banking customers enter their passwords exclusively […]
Hackers Use Ethereum Blockchain to Conceal C2 Infrastructure with EtherRAT Malware
Hackers Leverage EtherRAT and EtherHiding to Conceal Malware Infrastructure on Ethereum In a significant advancement in cyberattack methodologies, threat actors are deploying a sophisticated backdoor […]
Cybercriminals Use Telegram to Spread Advanced CrystalX Malware-as-a-Service Globally
Cybercriminals Exploit Telegram to Distribute CrystalX Malware-as-a-Service In the ever-evolving landscape of cyber threats, a new and formidable player has emerged: CrystalX, a Malware-as-a-Service (MaaS) […]