Anthropic CEO Dario Amodei Accuses OpenAI of Deceptive Practices in Military Agreement In a recent internal memo, Dario Amodei, co-founder and CEO of Anthropic, has […]
Month: March 2026
High-Severity XSS Flaw in Angular i18n Threatens Applications; Update Required
Critical XSS Vulnerability in Angular i18n Puts Applications at Risk A significant security flaw, identified as CVE-2026-27970, has been discovered in Angular’s internationalization (i18n) pipeline. […]
Microsoft’s October 2025 Update Disrupts Windows Recovery, Fix Released After Four Months
Microsoft’s October 2025 update, KB5068164, intended to enhance the Windows Recovery Environment (WinRE) on Windows 10 versions 21H2 and 22H2, inadvertently introduced a critical flaw […]
New VoidLink Malware Targets Kubernetes, AI Workloads with Advanced Evasion Tactics
VoidLink: The New Cloud-Native Malware Targeting Kubernetes and AI Workloads In December 2025, cybersecurity researchers uncovered a sophisticated malware framework named VoidLink, engineered specifically to […]
Critical VMware Aria Operations Vulnerability Exploited, CISA Urges Immediate Mitigation
Critical VMware Aria Operations Vulnerability Exploited: Immediate Action Required A significant security flaw has been identified in VMware Aria Operations, formerly known as vRealize Operations […]
Microsoft and Europol Dismantle Major 2FA Phishing Platform, Seize 330 Domains in Global Cybersecurity Effort
Microsoft and Europol Dismantle Tycoon 2FA Phishing Platform, Disrupting Global Cyber Threat In a significant blow to cybercriminal operations, Microsoft, in collaboration with Europol and […]
Ransomware Operators Exploit Microsoft’s AzCopy for Stealth Data Exfiltration in New Attack Method
Cybercriminals Exploit Microsoft’s AzCopy for Stealthy Data Theft in Ransomware Attacks In a concerning evolution of cyber threats, ransomware operators are now repurposing Microsoft’s AzCopy—a […]
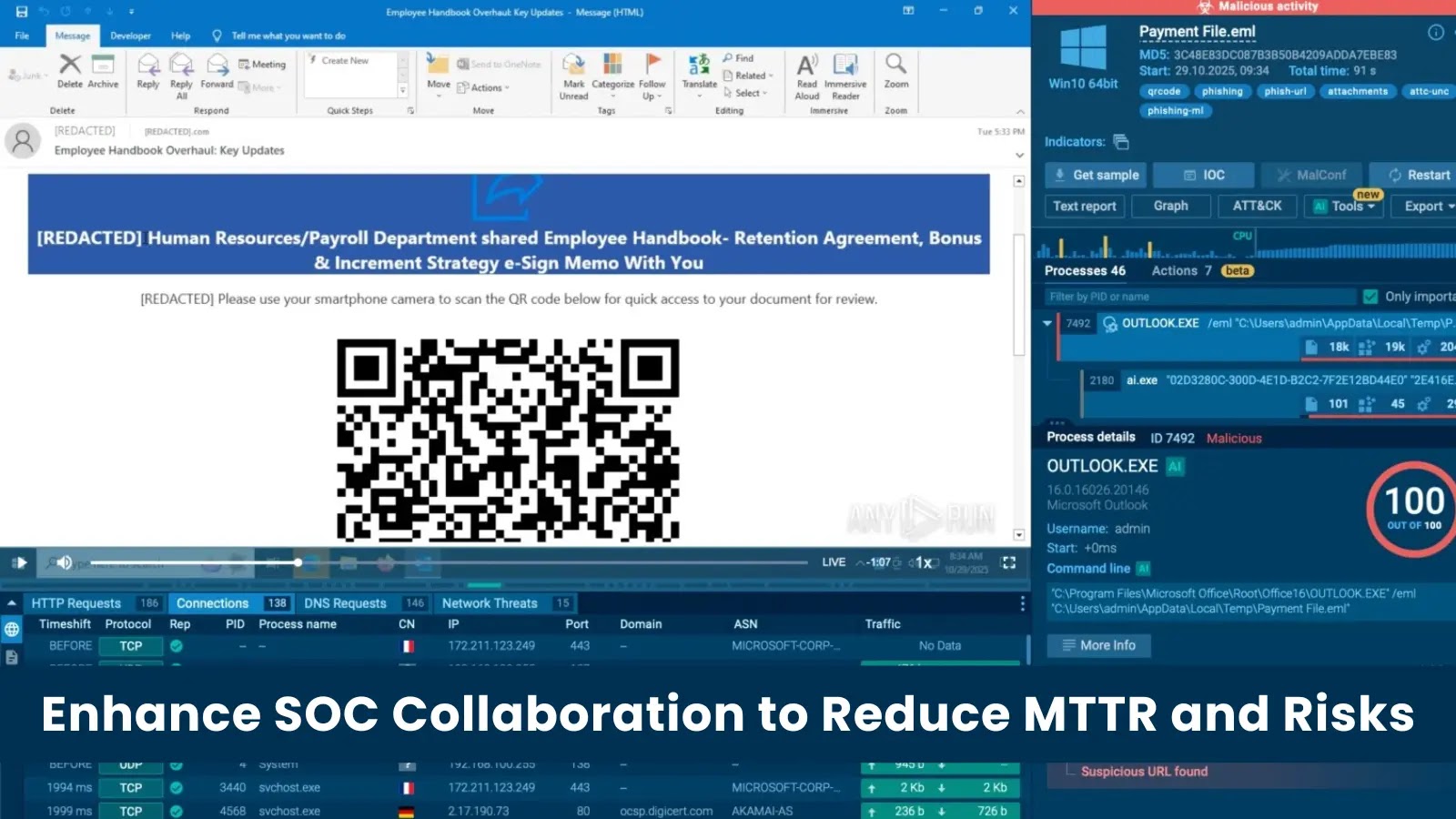
Streamlining SOC Operations: Key to Faster Threat Response and Lower Business Risks
Enhancing SOC Efficiency: The Key to Reducing MTTR and Business Risk In today’s fast-paced digital landscape, Security Operations Centers (SOCs) are under immense pressure to […]
Thousands of Honeywell BMS Controllers Vulnerable Online Due to Unauthenticated Access
Thousands of Honeywell Controllers Exposed Online Without Authentication Recent findings have revealed that thousands of Honeywell building-management controllers are accessible online without requiring authentication. This […]
Stolen Gemini API Key Results in $82,000 Charges for Mexican Team amid Cloud Security Lapses
Stolen Gemini API Key Leads to $82,000 in Unauthorized Charges for Mexican Development Team A small development team in Mexico, consisting of three members, is […]