Bumble Unveils ‘Bee’: Your AI-Powered Dating Companion In a bold move to redefine the online dating experience, Bumble has introduced ‘Bee,’ an AI-driven assistant designed […]
Month: March 2026
Startup Pioneers Seamless Integration of Quantum Computing for Enterprises
As the quantum computing landscape rapidly evolves, a pioneering startup is positioning itself to ensure enterprises are not just prepared but already operating within this […]
Atlassian to Lay Off 1,600 Employees, Shifts Focus to AI and Enterprise Sales Strategy
Atlassian’s Strategic Shift: Embracing AI Through Workforce Restructuring In a decisive move to realign its strategic priorities, Atlassian, the Australian software powerhouse renowned for products […]
Amazon Launches ‘Sassy’ Alexa+ Personality for Adults, Adds Humor and Wit with Enhanced Security
Amazon Introduces ‘Sassy’ Alexa+ Personality: A Bold New Voice for Adults Amazon has unveiled a new personality style for its AI assistant, Alexa+, called Sassy, […]
Grammarly Sued for Using Writers’ Identities Without Consent in AI Feature
Grammarly Faces Legal Action Over Unauthorized Use of Writers’ Identities in AI Feature Grammarly, a widely-used digital writing assistant, is currently embroiled in legal controversy […]
Critical Flaw in Splunk Allows Remote Command Execution, Urgent Patching Required
Critical Splunk Vulnerability Enables Remote Command Execution A significant security flaw has been identified in Splunk’s Enterprise and Cloud platforms, posing a substantial risk to […]
Critical SolarWinds Vulnerability Allows Remote Code Execution; CISA Urges Immediate Patch
Critical SolarWinds Web Help Desk Vulnerability Enables Unauthenticated Remote Code Execution A critical security vulnerability has been identified in SolarWinds Web Help Desk, designated as […]
Critical Flaw in Palo Alto Networks’ Cortex XDR Broker VM Exposes Sensitive Data, Urgent Patch Required
Critical Vulnerability in Palo Alto Networks’ Cortex XDR Broker VM Exposes Sensitive Information A significant security vulnerability has been identified in Palo Alto Networks’ Cortex […]
OpenSSH Vulnerability CVE-2026-3497 Puts Systems at Risk of Remote Exploitation and Privilege Bypass
Critical OpenSSH GSSAPI Vulnerability Exposes Systems to Remote Attacks A significant security flaw has been identified in the Generic Security Service Application Program Interface (GSSAPI) […]
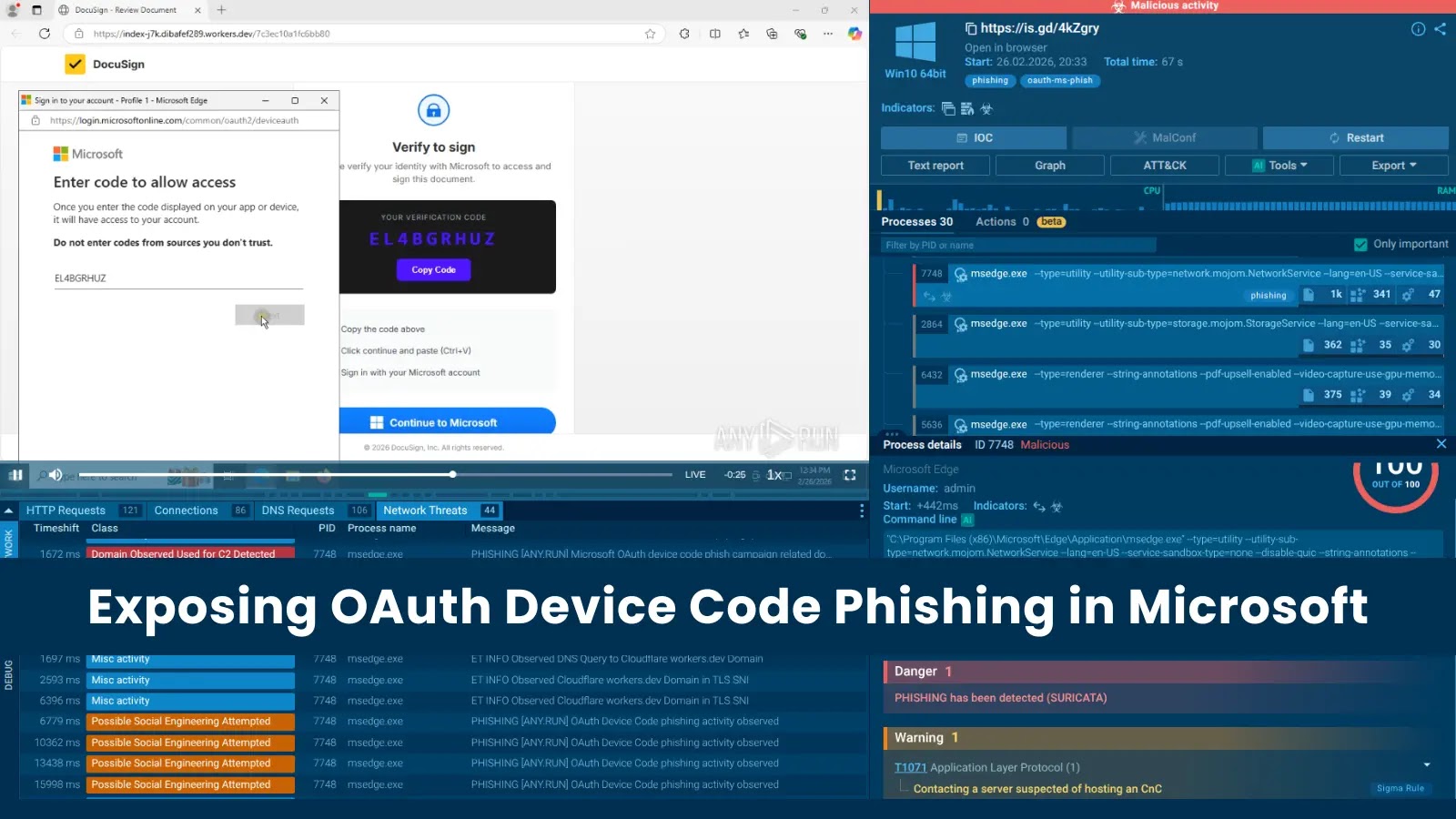
Phishing Attacks Exploit OAuth Device Code Flow, Bypassing MFA and Hijacking Microsoft 365 Accounts
Exploiting OAuth Device Code Flow: A New Frontier in Phishing Attacks In recent developments, cybersecurity experts have identified a surge in phishing campaigns that exploit […]