Vshell: The Emerging Threat Actor’s Tool of Choice Over Cobalt Strike In the ever-evolving landscape of cybersecurity threats, a new player has been gaining significant […]
Month: February 2026
U.S. Government Bans Anthropic AI, Cites National Security Risks
U.S. Government Bans Anthropic AI Over National Security Concerns In a decisive move, the United States government has ordered all federal agencies to cease using […]
Trend Micro Patches Critical Vulnerabilities in Apex One Allowing Remote Code Execution
Critical Vulnerabilities in Trend Micro Apex One Expose Systems to Remote Code Execution Trend Micro has recently addressed multiple critical vulnerabilities in its Apex One […]
Cybersecurity Researchers Unveil Aeternum C2: Blockchain-Based Botnet Loader Defies Traditional Takedown Methods
In a groundbreaking development, cybersecurity researchers have unveiled Aeternum C2, a botnet loader that leverages blockchain technology to establish a resilient and virtually indestructible command-and-control […]
Stealthy Dohdoor Malware Targets U.S. Schools and Healthcare, Leveraging Advanced Evasion Techniques
Dohdoor Malware: A Stealthy Threat Targeting U.S. Schools and Healthcare Institutions In recent months, a sophisticated cyber threat has emerged, targeting educational and healthcare institutions […]
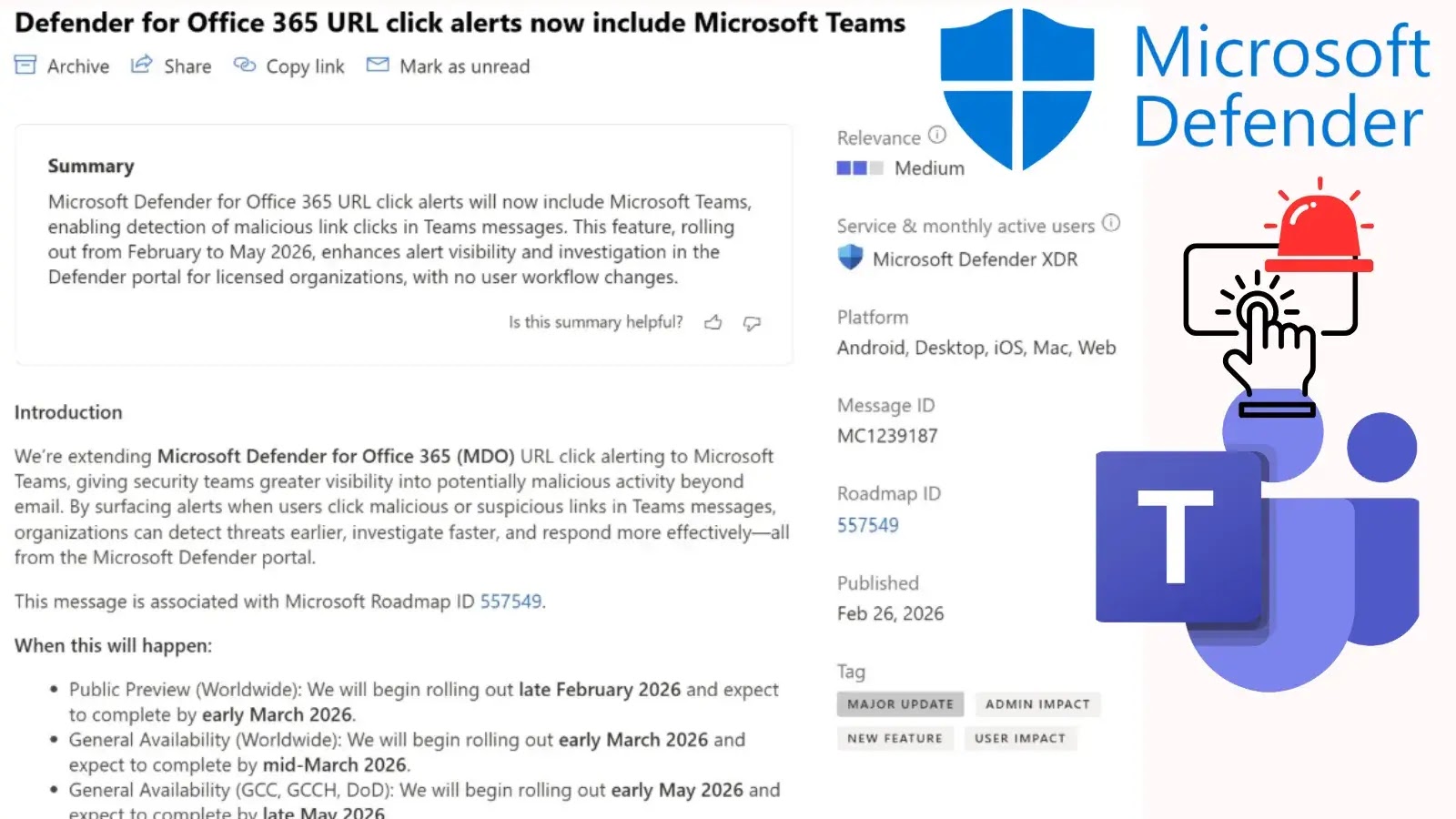
Microsoft Defender Expands URL Click Alerts to Microsoft Teams for Enhanced Security
Microsoft Defender Enhances Security by Extending URL Click Alerts to Microsoft Teams In a significant move to bolster cybersecurity defenses, Microsoft has expanded its Defender […]
Hackers Use Gaming Tools to Spread Remote Access Trojans in New Cyber Scheme
Cybercriminals Exploit Gaming Utilities to Deploy Remote Access Trojans In a recent cybersecurity development, attackers have been embedding malware within seemingly legitimate gaming utilities, compromising […]
Malicious Go Module Impersonates Trusted Library to Deploy Rekoobe Backdoor, Steal Credentials
Malicious Go Module Mimics Trusted Library to Steal Credentials and Deploy Rekoobe Backdoor A recently uncovered supply chain attack has placed Go developers at significant […]
Juniper Networks Alerts on Critical PTX Router Flaw Allowing Remote Takeover; Urges Immediate Update
Critical Juniper Networks PTX Vulnerability Exposes Routers to Full Remote Takeover Juniper Networks has recently identified a critical security flaw in its Junos OS Evolved […]
Infostealer Malware Fuels Brute-Force Attacks on Corporate SSO, Targets Multinational Firms and Police Agencies
Infostealer Malware Drives Large-Scale Brute-Force Attacks on Corporate SSO Gateways A recent surge in credential stuffing attacks has unveiled a concerning trend: cybercriminals are infiltrating […]