Apple’s Strategic Acquisition of invrs.io: Enhancing AI-Driven Photonics Research Introduction In a significant move to bolster its capabilities in artificial intelligence (AI) and photonics, Apple […]
Month: February 2026
Improving Cybersecurity Triage: Addressing Flaws to Cut Risks and Boost Efficiency
Enhancing Cybersecurity: Addressing the Pitfalls of Ineffective Triage In the realm of cybersecurity, triage is intended to streamline the process of identifying and addressing threats. […]
SolarWinds Urges Immediate Update for Serv-U to Patch Critical Security Flaws Enabling Root Access
SolarWinds Releases Critical Patches for Serv-U Vulnerabilities Enabling Root-Level Code Execution SolarWinds has recently issued critical updates to its Serv-U file transfer software, addressing four […]
Cybercrime Group SLH Recruits Women for Vishing Attacks, Offers $500–$1,000 Per Call
Cybercrime Group SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks The cybercrime collective known as Scattered LAPSUS$ Hunters (SLH) […]
National Security Urged to Automate Data Transfers as Manual Processes Pose Significant Risks
Automating Sensitive Data Transfers: A Mission-Critical Priority for National Security In today’s rapidly evolving digital landscape, the reliance on manual processes for transferring sensitive data […]
Malicious NuGet Packages Target ASP.NET Developers to Deploy Backdoors, Exfiltrate Data
Malicious NuGet Packages Compromise ASP.NET Applications and Deploy Backdoors Cybersecurity researchers have uncovered a series of malicious NuGet packages specifically designed to target ASP.NET web […]
Defense Contractor Employee Sentenced for Selling Zero-Day Exploits to Russian Broker
Defense Contractor Employee Sentenced to Over Seven Years for Selling Zero-Day Exploits to Russian Broker In a significant case highlighting the risks of insider threats […]
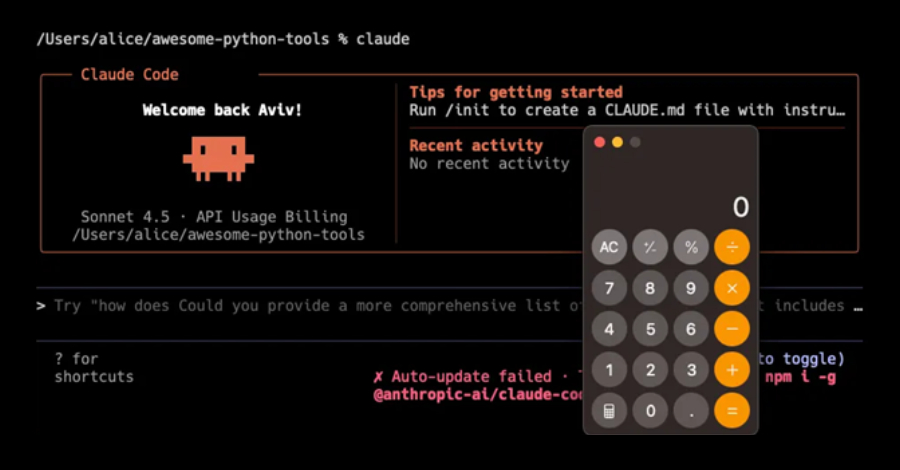
Critical Vulnerabilities in Claude Code Enable Remote Code Execution and API Key Theft
Critical Vulnerabilities in Claude Code Expose Systems to Remote Code Execution and API Key Theft Recent investigations have uncovered significant security vulnerabilities within Anthropic’s AI-driven […]
CISA Confirms Active Exploitation of Critical FileZen Vulnerability CVE-2026-25108
CISA Confirms Active Exploitation of FileZen CVE-2026-25108 Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently added a critical vulnerability in Soliton Systems’ […]
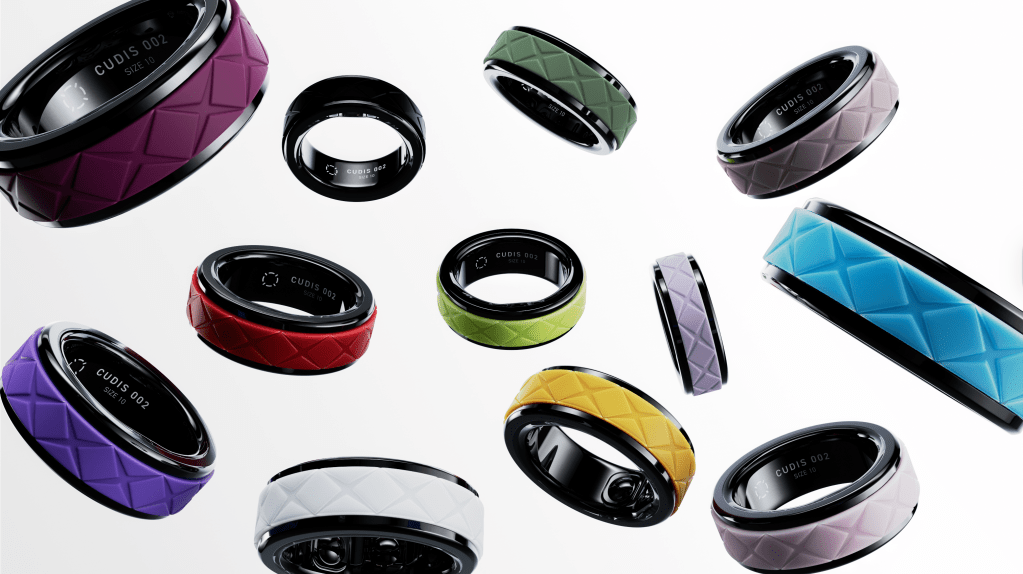
CUDIS Launches AI-Driven Health Ring with Personalized Coaching and Rewards System
CUDIS Unveils Advanced Health Ring with AI-Powered Coaching and Reward System In a significant advancement in wearable health technology, CUDIS has introduced its latest series […]