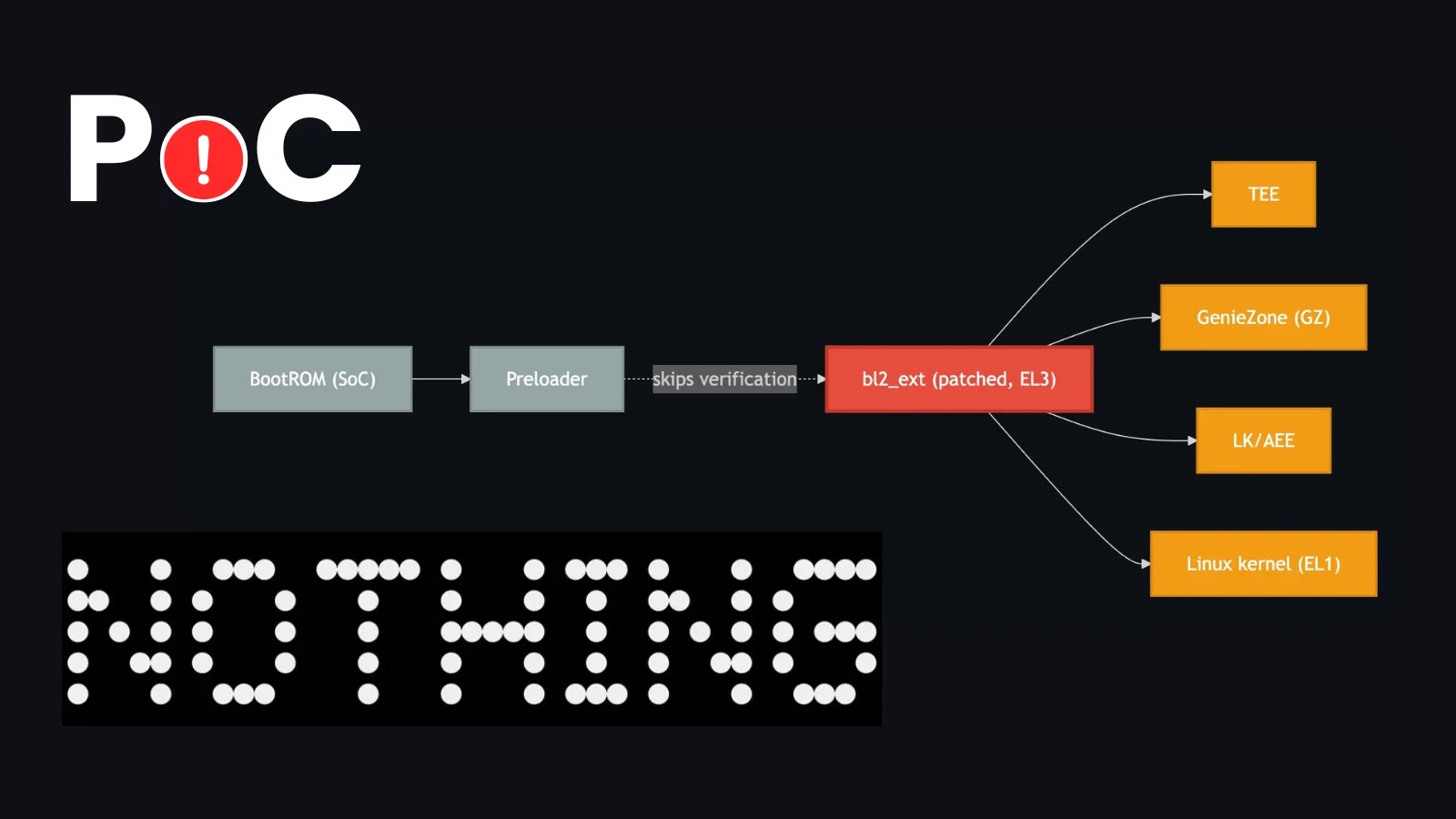
A recently disclosed proof-of-concept (PoC) exploit, named Fenrir, has unveiled a critical vulnerability within the secure boot process of the Nothing Phone (2a) and CMF […]
Year: 2025
Shuyal Stealer: A Sophisticated Threat Targeting 19 Web Browsers
In the ever-evolving landscape of cyber threats, a new and formidable adversary has emerged: Shuyal Stealer. First identified in early August 2025, this malware has […]
Microsoft Events Platform Vulnerability Exposes User Data
A critical security vulnerability was identified within Microsoft’s Events platform, potentially allowing unauthorized access to users’ personal information stored in both event registration and waitlist […]
Microsoft 365 Outage Disrupts Access to Admin Center, Services, and Entra ID
On October 9, 2025, a significant outage affected Microsoft’s cloud-based productivity suite, Microsoft 365, rendering the admin center and various services reliant on Microsoft Entra […]
Microsoft Azure Global Outage Disrupts Services Across Europe and Africa
On October 9, 2025, Microsoft Azure, a leading cloud computing platform, experienced a significant service disruption that affected customers across Europe and Africa. The outage […]
Emergence of ‘Trinity of Chaos’ Hacker Alliance: Data Breach Impacts 39 Major Corporations
The cybersecurity community is currently grappling with the rise of a formidable hacker alliance known as ‘Trinity of Chaos.’ This collective has recently unveiled a […]
Exploiting AI Chatbots: A New Frontier for Cyber Intrusions
In recent weeks, cybersecurity experts have identified a sophisticated malware campaign that exploits conversational AI chatbots as covert gateways into enterprise systems. First detected in […]
SonicWall Confirms Theft of Customer Firewall Configuration Backups
SonicWall, a prominent cybersecurity firm, has disclosed a significant security breach involving the unauthorized access and theft of customer firewall configuration backup files from its […]
Emergence of Automated Phishing Kits: The Rise of ClickFix Attacks
The cybersecurity landscape is witnessing a significant shift with the advent of automated phishing toolkits, notably the IUAM ClickFix Generator. This development enables individuals with […]
Cybercriminals Exploit Velociraptor DFIR Tool in Sophisticated Ransomware Attacks
In recent cybersecurity developments, threat actors have been observed repurposing Velociraptor, an open-source Digital Forensics and Incident Response (DFIR) tool, to facilitate complex ransomware attacks. […]