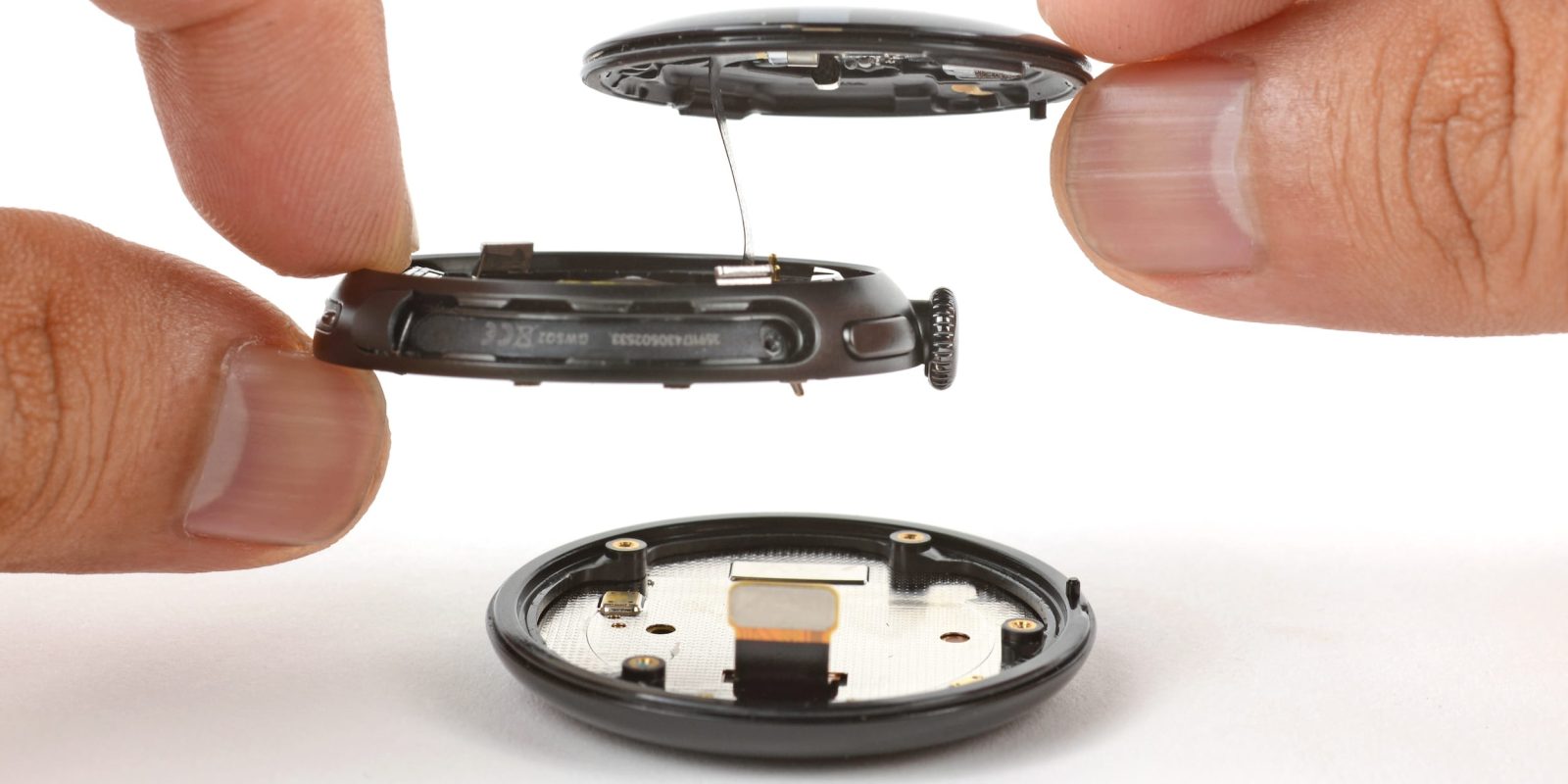
Google’s Pixel Watch 4 marks a significant advancement in smartwatch design, emphasizing both user-friendly repairability and enhanced functionality. This shift addresses previous criticisms regarding the […]
Year: 2025
Chrome Enhances User Experience by Automatically Disabling Notifications from Infrequently Visited Sites
In an effort to streamline user interactions and minimize the inundation of notifications, Google has introduced a new feature in its Chrome browser for both […]
Google’s ‘Berry’ Color: A Call for a Red Pixel Phone
Google has consistently explored diverse color palettes for its Pixel smartphones, introducing shades like Indigo and Coral in recent models. However, the recent unveiling of […]
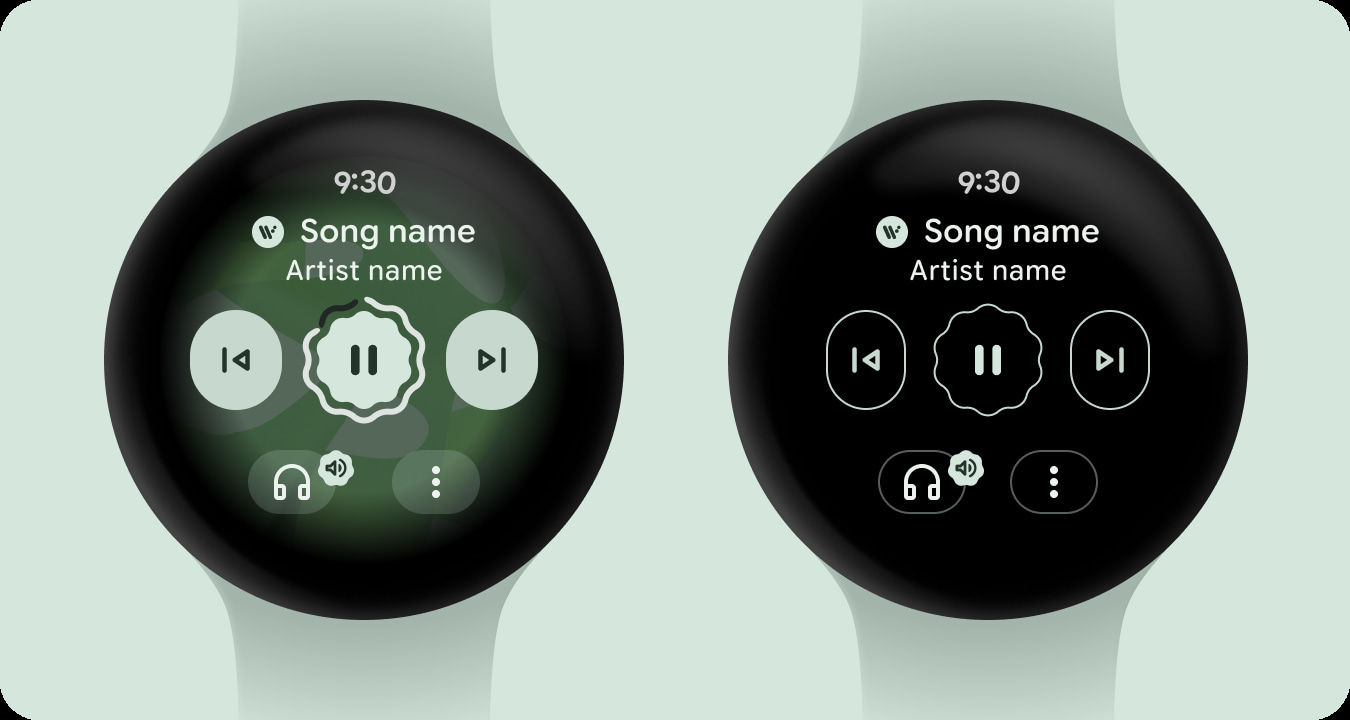
Pixel Watch to Introduce Always-On Display Media Controls with Wear OS 6
Google’s Pixel Watch series is set to receive a significant enhancement with the upcoming Wear OS 6 update, introducing always-on display (AOD) media controls. This […]
[October-10-2025] Daily Cybersecurity Threat Report
This report details a series of recent cyber incidents, providing key information for each event, including published URLs and associated screenshots, strictly based on the […]
Critical Vulnerability in WordPress Service Finder Theme Allows Unauthorized Access
A significant security flaw has been identified in the Service Finder WordPress theme, enabling unauthorized users to gain full control over affected websites. This vulnerability, […]
AI’s Dual Role in Cybersecurity: A Double-Edged Sword
Artificial Intelligence (AI) has become a pivotal force in the realm of cybersecurity, serving both as a formidable tool for defense and a potent weapon […]
Understanding Token-Based SaaS Breaches: A Guide for Security Teams
In the modern digital landscape, organizations heavily depend on Software-as-a-Service (SaaS) applications to streamline operations and enhance productivity. Central to the functionality of these applications […]
Emerging Cyber Threats: Microsoft Teams Exploits, MFA Bypass Techniques, and AI-Driven Disinformation Campaigns
In the rapidly evolving landscape of cybersecurity, recent developments have highlighted sophisticated methods employed by threat actors to exploit widely used platforms and technologies. This […]
SonicWall Cloud Backup Breach: A Comprehensive Analysis and Mitigation Guide
In early October 2025, SonicWall, a prominent provider of network security solutions, disclosed a significant security incident involving unauthorized access to firewall configuration backup files […]


![[October-10-2025] Daily Cybersecurity Threat Report](https://thedailytechfeed.com/wp-content/uploads/2025/04/s1.jpg)