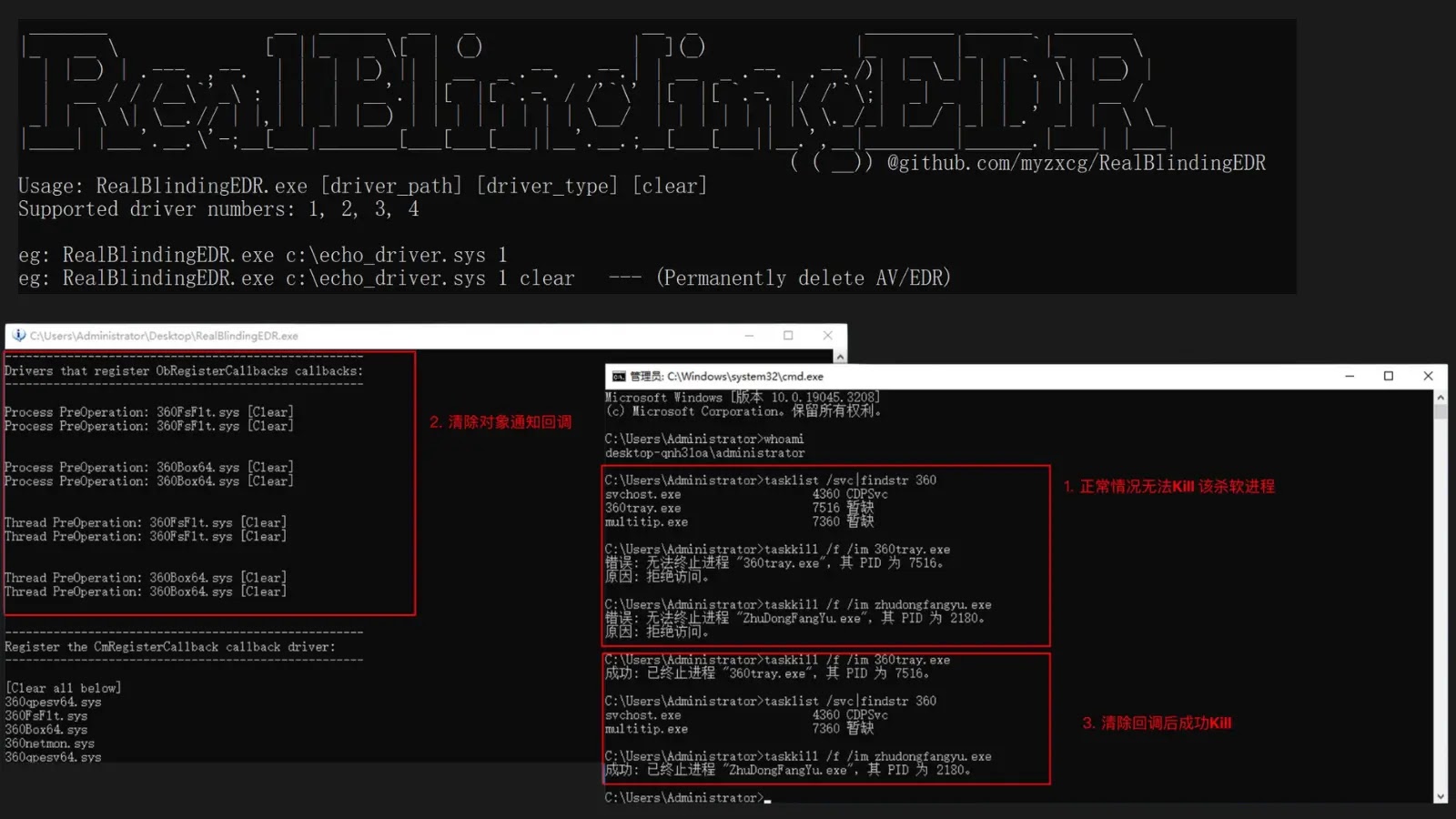
In late 2023, a tool named RealBlindingEDR emerged on GitHub, offering the capability to disable antivirus (AV) and endpoint detection and response (EDR) systems on […]
Year: 2025
Stealit Malware Exploits Node.js SEA to Target Windows Systems
A sophisticated malware campaign known as Stealit has recently emerged, targeting Windows systems by exploiting the Node.js Single Executable Application (SEA) feature. This approach allows […]
Critical Vulnerability in Happy DOM Exposes Millions to Remote Code Execution Risks
A critical security vulnerability has been identified in Happy DOM, a widely used JavaScript Document Object Model (DOM) implementation, affecting all versions up to v19. […]
Unveiling EDR-Freeze: A Novel Technique to Temporarily Suspend Security Software
In the ever-evolving landscape of cybersecurity, adversaries continually develop sophisticated methods to circumvent protective measures. A recent analysis by researcher Itamar Hällström has shed light […]
Cybercriminals Exploit Discord Webhooks for Covert Command-and-Control in npm, PyPI, and RubyGems Packages
In recent developments, cybercriminals have innovatively repurposed Discord webhooks as clandestine command-and-control (C2) channels across various programming language ecosystems, including npm, PyPI, and RubyGems. This […]
Critical Vulnerability in AMD SEV-SNP Exposes Confidential Data to Potential Exfiltration
A significant security flaw has been identified in AMD’s Secure Encrypted Virtualization with Secure Nested Paging (SEV-SNP), a technology integral to confidential computing environments utilized […]
Astaroth Banking Trojan Exploits GitHub to Conceal Malicious Configurations
A new variant of the Astaroth banking trojan has surfaced, employing innovative tactics to distribute its malicious configuration files. First identified in late 2025, this […]
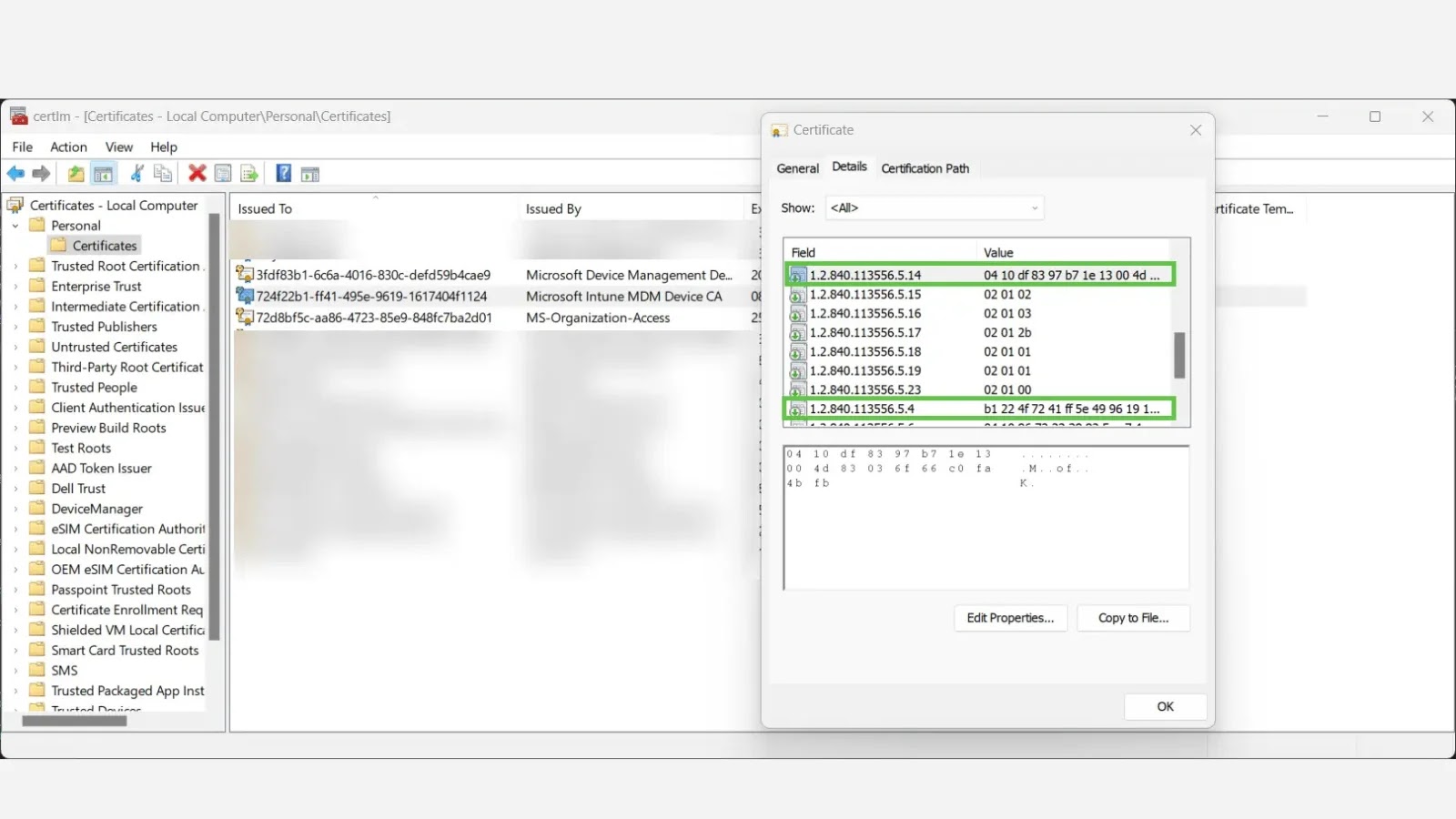
Enhancing Device Identity Verification with Microsoft Intune MDM and Entra ID
Recent research has unveiled a more reliable method for verifying device and tenant identities by leveraging Microsoft Intune’s Mobile Device Management (MDM) certificates. This approach […]
Scattered Lapsus$ Hunters Claim to Have Stolen Over 1 Billion Salesforce Records
In a significant escalation of cybercriminal activity, the group known as Scattered Lapsus$ Hunters has announced the exfiltration of more than one billion records from […]
Linux Kernel 6.18-rc1 Released: A Comprehensive Overview of New Features and Enhancements
On October 12, 2025, Linus Torvalds announced the release of Linux Kernel 6.18-rc1, marking the commencement of the release candidate phase for this upcoming kernel […]