Since at least 2018, a clandestine network of North Korean IT operatives has been infiltrating global technology and infrastructure companies by posing as legitimate freelancers. […]
Year: 2025
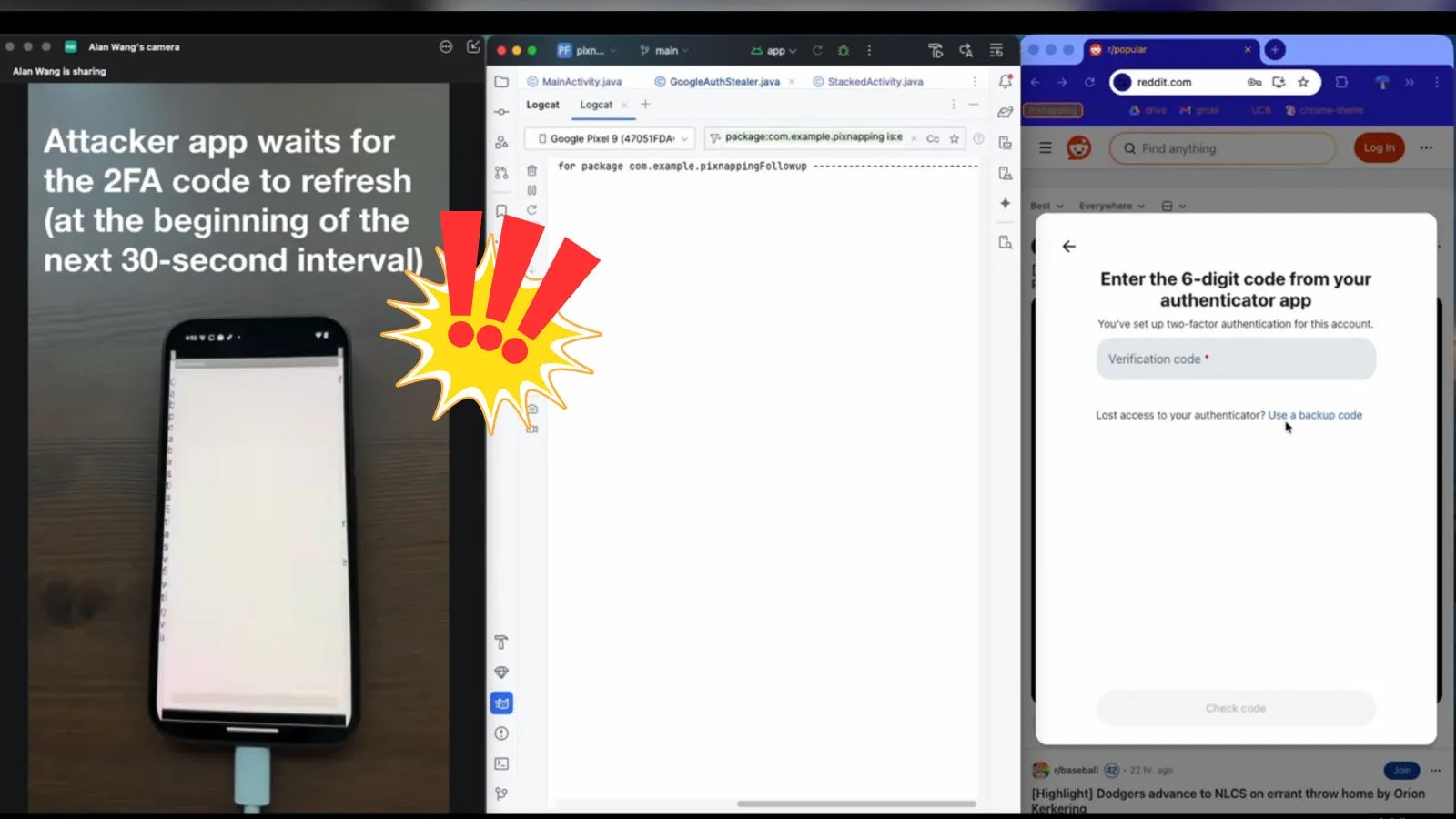
Pixnapping: A New Threat to Android Security
A newly identified security vulnerability, termed Pixnapping, poses a significant risk to Android devices by enabling malicious applications to covertly extract sensitive on-screen information. This […]
Critical UEFI Shell Vulnerabilities Expose Over 200,000 Laptops to Secure Boot Bypass
Recent findings have unveiled significant vulnerabilities within signed UEFI shells, potentially allowing attackers to circumvent Secure Boot protections on more than 200,000 Framework laptops and […]
Cybercriminals Impersonate OpenAI and Sora Services to Harvest Login Credentials
In recent weeks, a sophisticated phishing campaign has emerged, targeting both corporate and individual accounts by masquerading as legitimate OpenAI and Sora login portals. Attackers […]
Microsoft Ends Windows 10 Support: What Users Need to Know
As of October 14, 2025, Microsoft has officially ended support for Windows 10, concluding a decade-long era for one of the most widely used operating […]
Critical FortiOS CLI Vulnerability Allows Unauthorized System Command Execution
On October 14, 2025, Fortinet disclosed a significant security vulnerability in its FortiOS operating system, identified as CVE-2025-58325. This flaw enables local authenticated attackers to […]
Microsoft’s October 2025 Patch Tuesday Addresses 172 Vulnerabilities, Including Four Zero-Day Flaws
On October 14, 2025, Microsoft released its latest Patch Tuesday updates, addressing a substantial 172 vulnerabilities across its product suite. This comprehensive update includes fixes […]
Critical Authentication Bypass Vulnerability in FortiPAM and FortiSwitch Manager Exposes Systems to Remote Attacks
Fortinet, a leading cybersecurity solutions provider, has issued an urgent advisory regarding a critical vulnerability in its FortiPAM and FortiSwitch Manager products. This flaw, identified […]
Cybercriminals Exploit Fake Judicial Notifications to Deploy Info-Stealer Malware
Cybercriminals have launched a sophisticated phishing campaign targeting Colombian users by sending fraudulent judicial notifications. This multi-stage attack culminates in the deployment of AsyncRAT, a […]
Sophisticated Phishing Campaign Exploits NPM Ecosystem to Target Developers
In October 2025, cybersecurity researchers identified a sophisticated phishing campaign that exploits the NPM (Node Package Manager) ecosystem in an unprecedented manner. Unlike traditional attacks […]