A sophisticated cyberattack campaign has been identified, targeting macOS users through counterfeit Homebrew installer websites. These deceptive sites deliver malicious payloads alongside the legitimate Homebrew […]
Year: 2025
Russian Cybercriminals Shift from RDP Access Sales to Malware Stealer Logs
The Russian cybercrime landscape is undergoing a significant transformation. Cybercriminals are moving away from selling compromised Remote Desktop Protocol (RDP) access and are now focusing […]
Critical Vulnerability in Elastic Cloud Enterprise Allows Malicious Command Execution
Elastic has recently disclosed a critical security vulnerability in its Elastic Cloud Enterprise (ECE) platform, identified as CVE-2025-37729. This flaw enables administrators with malicious intent […]
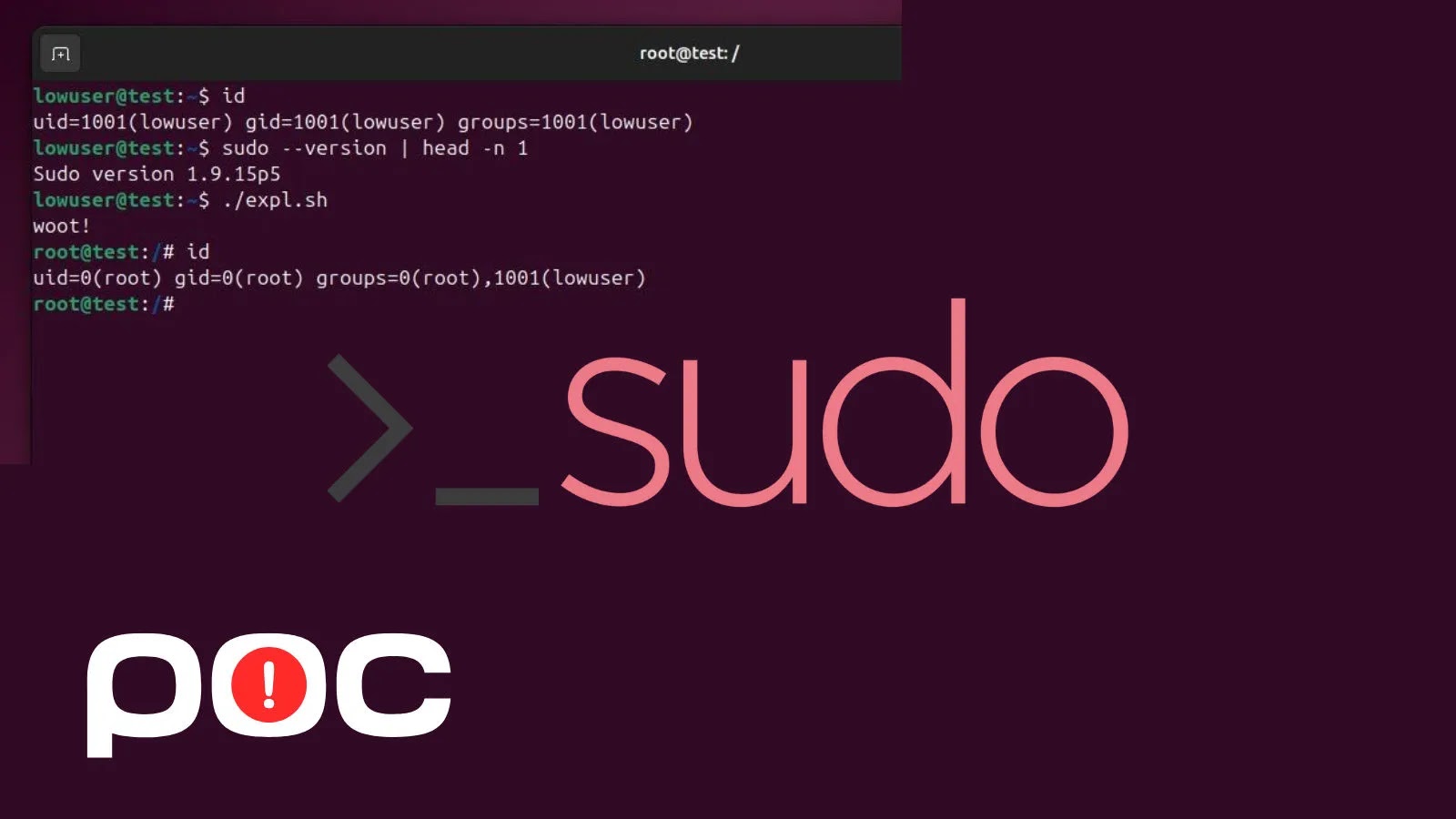
Critical Sudo Chroot Vulnerability Exposes Linux Systems to Root Privilege Escalation
A significant security flaw has been identified in the Sudo utility, a fundamental tool in Unix-like operating systems, following the public release of a proof-of-concept […]
Ivanti Addresses 13 Critical Vulnerabilities in Endpoint Manager to Prevent Remote Code Execution
Ivanti, a prominent provider of IT asset and endpoint management solutions, has recently disclosed 13 vulnerabilities within its Endpoint Manager (EPM) software. Among these, two […]
Threat Actors Exploit ScreenConnect for Unauthorized Remote Access
Remote Monitoring and Management (RMM) tools are essential for IT administrators, enabling efficient remote control, unattended access, and automated tasks across enterprise systems. However, recent […]
SimonMed Data Breach Exposes 1.2 Million Patients’ Sensitive Information
SimonMed Imaging, a prominent provider of outpatient medical imaging services in the United States, has reported a significant cybersecurity incident that compromised the personal and […]
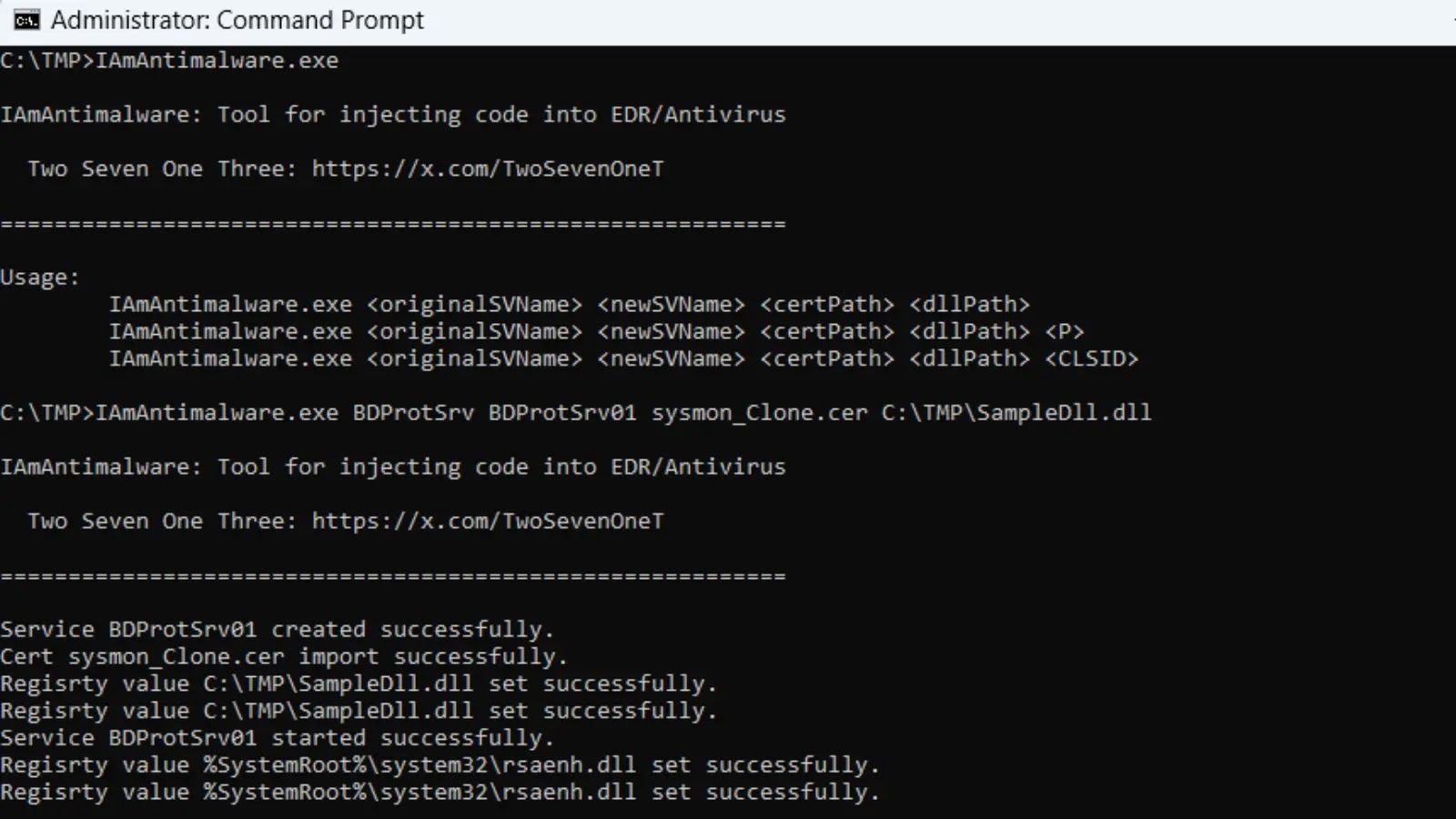
Emergence of IAmAntimalware: A Tool That Turns Antivirus Software into Potential Threats
A newly developed tool named IAmAntimalware has surfaced, capable of injecting malicious code directly into antivirus software processes. This tool, released on October 11, 2025, […]
Massive Data Exposure: Over 178,000 Invoices with Sensitive Customer Information Leaked by Invoicely
In early October 2025, cybersecurity researcher Jeremiah Fowler uncovered a significant data exposure involving Invoicely, a Vienna-based invoicing and billing platform utilized by more than […]
TA585’s Innovative Web Injection Tactics Deploy MonsterV2 Malware on Windows Systems
The cybersecurity landscape is continually evolving, with threat actors developing increasingly sophisticated methods to compromise systems. A newly identified cybercriminal group, designated TA585, has emerged […]