A significant security flaw has been identified in ICTBroadcast, an autodialer software developed by ICT Innovations, which is currently being actively exploited by cyber attackers. […]
Year: 2025
Critical Vulnerabilities in Red Lion RTUs Pose Severe Industrial Control Risks
Recent cybersecurity research has unveiled two critical vulnerabilities in Red Lion’s Sixnet remote terminal units (RTUs), devices integral to industrial automation and control systems. These […]
Critical Windows Zero-Day Vulnerabilities Exploited in the Wild
On October 15, 2025, Microsoft released security updates addressing 183 vulnerabilities across its product suite. Among these, three zero-day vulnerabilities have been identified as actively […]
Understanding the Vulnerabilities in Synced Passkeys and Their Implications for Enterprise Security
In the evolving landscape of digital authentication, passkeys have emerged as a promising alternative to traditional passwords, offering enhanced security and user convenience. However, the […]
Over 100 VS Code Extensions Leak Access Tokens, Posing Supply Chain Threats
Recent research has revealed that over 100 Visual Studio Code (VS Code) extensions have inadvertently exposed access tokens, creating significant software supply chain vulnerabilities. These […]
Nation-State Hackers Breach F5 Networks, Exposing BIG-IP Source Code
In August 2025, F5 Networks, a prominent U.S. cybersecurity firm, identified a significant security breach within its systems. The intrusion, attributed to a highly sophisticated […]
Chinese Cyber Espionage Group ‘Jewelbug’ Infiltrates Russian IT Network for Five Months
A Chinese-linked cyber espionage group, known as ‘Jewelbug,’ has been implicated in a prolonged intrusion into a Russian IT service provider’s network, spanning from January […]
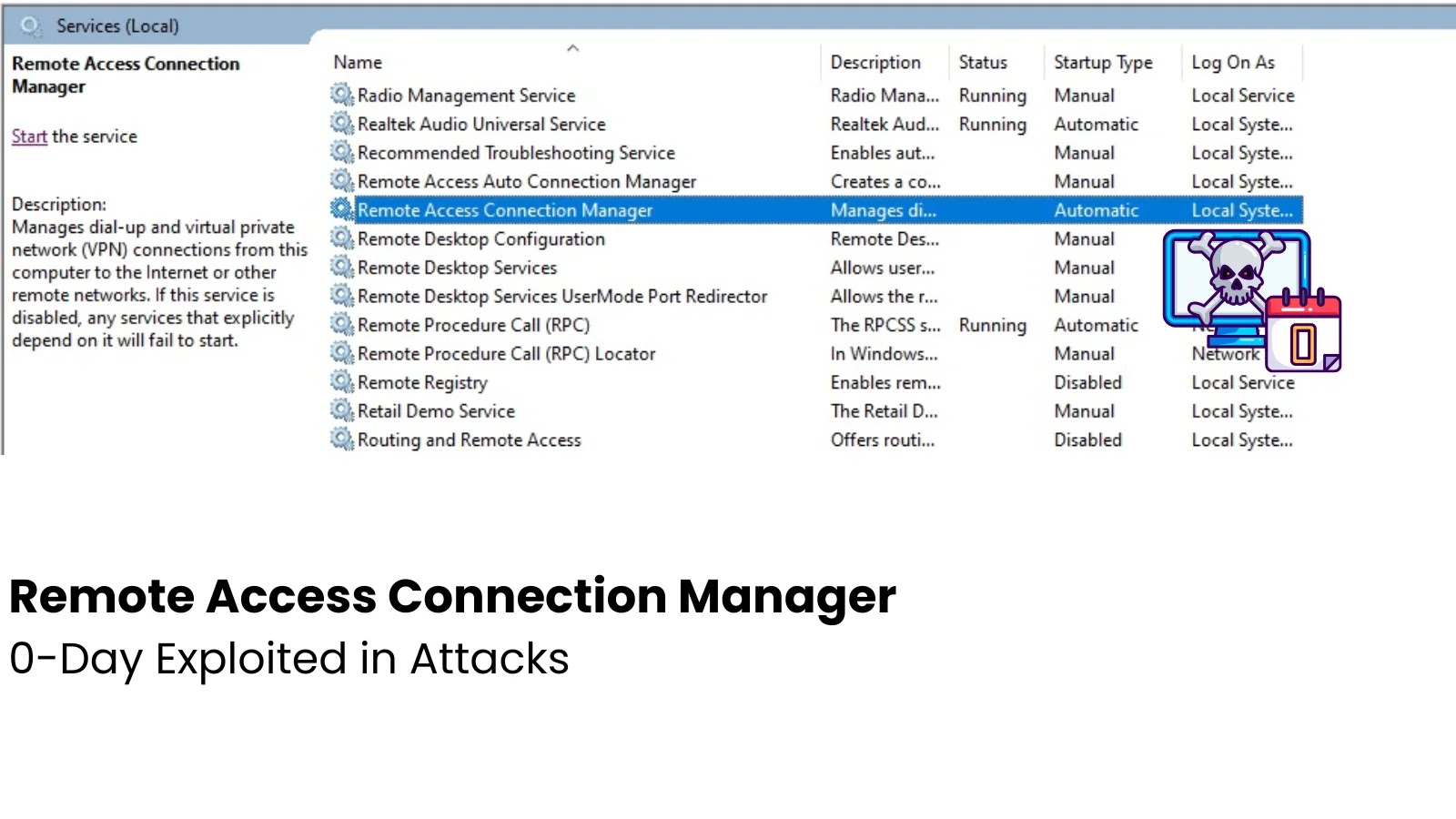
Critical Zero-Day Vulnerability in Windows Remote Access Connection Manager Actively Exploited
Microsoft has recently confirmed the active exploitation of a critical zero-day vulnerability within the Windows Remote Access Connection Manager (RasMan) service. This flaw, identified as […]
Google Releases Critical Chrome Update to Patch High-Severity Use-After-Free Vulnerability
Google has issued an urgent security update for its Chrome browser, addressing a high-severity use-after-free vulnerability that could allow attackers to execute arbitrary code on […]
Critical Vulnerability in Windows Remote Desktop Client Allows Remote Code Execution
On October 14, 2025, Microsoft disclosed a significant security flaw in its Remote Desktop Client, identified as CVE-2025-58718. This vulnerability arises from a use-after-free error, […]